- Overview
- Severity Threat Level Severity Definitions and Responses
- Automated Configuration with Learning Mode
- Deployment Overview with Learning Mode
- Threat Detector Threshold Manual Configuration and Definitions
- How to change Threat Detection Settings
- How to Enable “Monitor Only Mode” to Disable User lockout Actions
- How to Enable/Disable Critical Event Severity Detection
- How to Disable Snapshot Action for all Detections
Sub Topics
- How to Configure Monitor Mode and Ignored Lists
- How To Manage False Positives and Learning Mode
- Banned and Allowed File Type Configuration
- Rapid Machine to Machine Malware Spreading Attack Defense
- How to Manage Threat Detectors - Advanced Consult Support
- How to Configure Snapshot Modes (Critical Path and SMB share snapshots) and Snapshot Quotas
Overview
The detection of a Ransomware event will be contained strictly to the ECA nodes. Ransomware Defender will be responsible for taking action against the users access to cluster data and notifying administrators. This section identifies the behaviors that the Ransomware Defender takes when the ECA identifies a threat and how to configure settings that align to your company security policies or risk tolerance.
This section explains how to understand the settings and the impact of making changes to the detection settings and is provided as a reference. The recommended settings are defined in the Tuning Ransomware Defender Detections for Your Environment and changes to these settings should be done by consulting with support.
Severity Threat Level Severity Definitions and Responses
There are three Signal Strength Threshold levels defined, and Ransomware Defender will take different actions for each:
Automated Configuration with Learning Mode
This new mode requires 2.5.7 or later release and automates all aspects of customizing settings based a mode that learns about applications, and user behaviors used in each environment that Ransomware Defender is deployed.
Deployment Overview with Learning Mode
- This new mode will change the deployment process to enable monitor mode and then enable learning mode after deployment.
- After deployment monitor mode and learning mode are enabled by default.
- Wait 2-3 days after deployment to review settings that have been auto applied by Learning mode. Learning mode should be left enabled for a normal work flow time period to allow it to "see" all the work flows in your environment.
- Login to Ransomware Defender --> settings section
- View the learned Thresholds tab and review all users listed.
- If any of the listed users are application server service accounts. Then create a monitor only mode entry for this service account. This will disable lockouts but still alert and snapshot. See the guide here how to add monitor mode user account. Repeat for each service account.
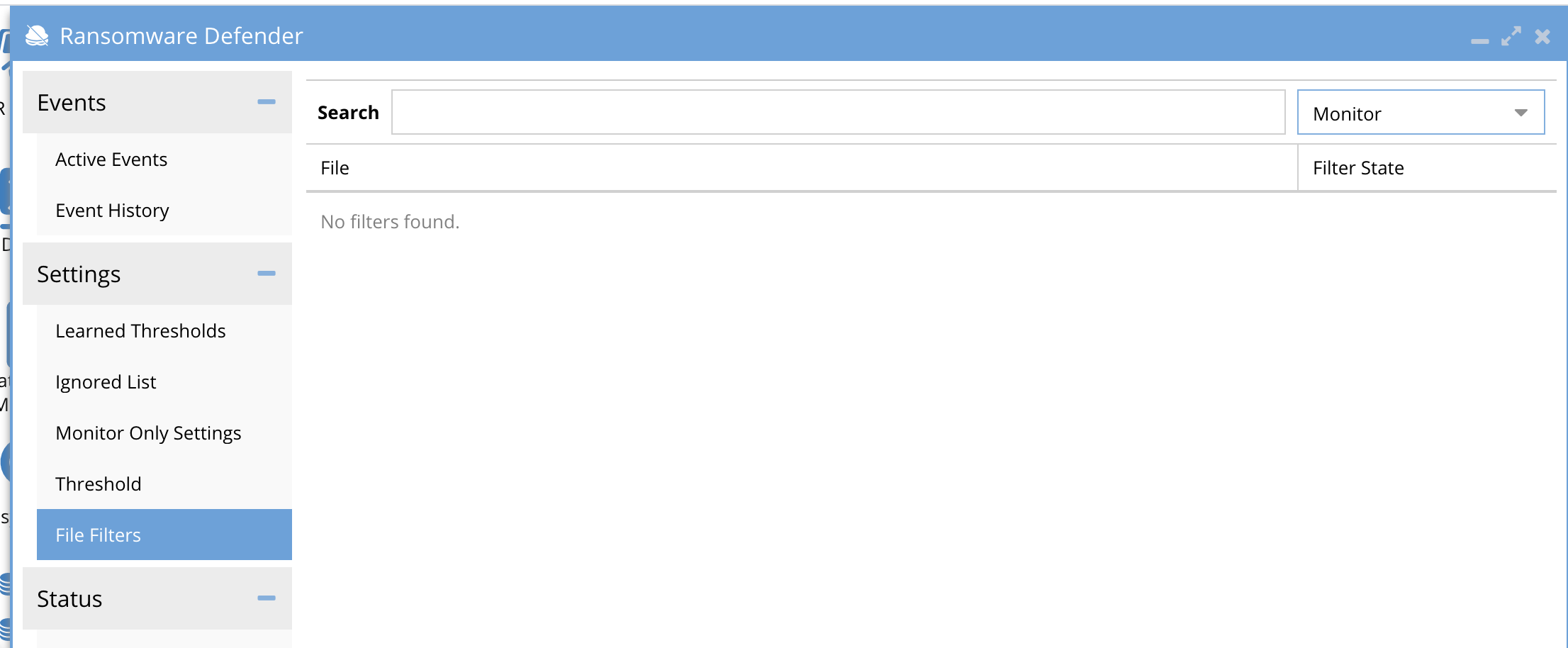
- View the File Filters tab
- Filter the list based on the monitor status. This status is set by learning mode when a user detection is based on a banned file extension. These detections will set the extension to monitor state (alert, snapshot no lockout)
- Review the list of application extensions to verify each extension listed is a legitimate application used in your environment.
- For applications that are legitimately using an extension on the banned list, change the state to disabled (this allows the file extension use and will be ignored for future detections). Make sure to click save.
- Leaving an extension in monitor state means it will still trigger detections and snapshots but no user lockout will occur. Leave this state if you are unsure about this extension in your environment.
- To switch the extension from monitor state to enforcement mode change the state to enabled and click save. Make this change to enabled state when you want this extension to trigger a user lockout.
- For application extensions that do not appear to be legitimate in your environment you should investigate the application extension to verify it is not a Ransomware detection.
- If you have custom extensions that you want to add, use the add button. NOTE: Use with caution, this will lockout users if in enabled status.
- Filter the list based on the monitor status. This status is set by learning mode when a user detection is based on a banned file extension. These detections will set the extension to monitor state (alert, snapshot no lockout)
- View the learned Thresholds tab and review all users listed.
- Exit Learning mode after the above steps are completed. How to disable learning mode.
Threat Detector Threshold Manual Configuration and Definitions
Ransomware Defender allows the administrator to configure the thresholds to determine what actions are taken based on crossing the thresholds. For a detailed explanation on how detection works see this section.
- Different thresholds are available for the WARNING, MAJOR, and CRITICAL severities of a detection.
- The MAJOR severity also allows the specification of the Grace Period (the time between event detection and lockout). Timed Lockout can be stopped with action menu on an active event.
The figure below shows the settings UI.
.png)
How to change Threat Detection Settings
- Open Ransomware Icon
- Click the Settings tab --> thresholds change the thresholds and click submit to save the settings.
This setting will advance all warning events from Warning to Major. This assumes that many warnings in a short period of time is suspicious and promotes all Warning events to a Major severity. This accelerates the response if a large number of users enter the Warning detection level even though the Major Signal Strength Threshold has not been crossed.
For example, based on the above settings, if there were 5 Active Events at the Warning threshold for different users, those events would be advanced to Major severity, even though the Signal Strength for any of those events had not met the 12 Signals in 1 minutes Major Threshold configuration.
Upgrade to Critical (events)
This setting will advance an event from Major to Critical for the case where the number of users configured here has an active Major event even though the Critical Signal Strength Threshold has not been crossed. This assumes that many Major detections is suspicious and promoting the severity to lockout the users sooner as a proactive response to protect file system data.
For example, based on the above settings, if there were 8 Active Events at the Major threshold for different users, those events would be advanced to Critical severity even though the Signal Strength for any of those events had not met the 30 Signals in 3 minute Critical Threshold configuration.
- The lower the Signal Strength Threshold the more sensitive the detection will become. Changing to a larger number can avoid false positives depending on IO patterns within your PowerScale environment.
- The Grace Period (minutes) sets how long a Major security event detection will wait before locking out the user named in the security event.
- Best practice: This should be set to a value that ensures an administrator can review the event and determine if lockout should occur or be canceled. It is the response to review an event before the lockout occurs.
- NOTE: Recommended to consult support before making any changes.
How to Enable “Monitor Only Mode” to Disable User lockout Actions
Monitor mode is used after installation to disable any actions for Major and Critical events and to baseline the environment. It can also be used to quickly disable user actions if too many false positives are detected. All detections will continue to alert administrators but no action will be taken to lockout. Snapshots will still be applied during detections.
See steps to enable monitor mode and enter enforcement mode.
How to Enable/Disable Critical Event Severity Detection
This option will disable immediate lockout action and will only use the major timed lockout option. This is recommended if risk tolerance for a lockout on users should be reviewed by an administrator, using the timed out lockout feature on Major severity detection.
NOTE: For this setting to take effect all active events must be archived as resolved or unresolved before changing the mode.
- Open Ransomware Defender window.
- Under Settings Thresholds
- Select the checkbox “Critical on Mode” so it is unchecked and click submit to save.
- This will disable the automatic lockout feature if the signal threshold is reached for Critical and means only delayed lockout Major severity will be the highest level of user action response.
- Done.
.png)
How to Disable Snapshot Action for all Detections
This is not recommended for normal operations. Snapshots are critical part of the solution for data recovery. Consult with support before disabling.
- Open Ransomware Defender icon
- Under settings, thresholds window
- Uncheck Create Snapshot
.png)