Current Release - Release Notes Ransomware Defender
| Release date | Version |
|---|---|
| 08/26/2024 | 2.9.0-24142 |
Article Navigation
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.9.0
- New in 2.9.0
- Fixed in 2.9.0
- DS-892 NFS lockout/restore for multiple zones failing - Powerscale only.
- DS-893 Eyeglass is trying to lockout access on an Export that was removed.
- DS-130 Critical Snapshots are not created using the RWS Sera API
- RWD-547 ECS Ransomware Defender SecurityGuard uses port 9020 instead of 9021.
- DS-125 Critical path - Cannot add same path/user for different platforms
- DS-126 Prevent Security Guard job to run in parallel on two devices
- DS-127 New UI - SG Alerts show as Critical in Alert Detail
- DS-89 [Qumulo]Create SMB share for security guard
- Known Issues
- DS-969 - [VAST]: Monitor Only List- rsw events from added paths is received as warning/major/critical if path is entered in the format 'tenant:/path/to/object'
- DS-970 - [QUMULO]: Monitor Only List- username field is case sensitive
- DS-1051 - [Powerscale] NFS lockout does not lockout the export without an IP added
- DS-1056 - [ECS] CRM Recovered count is not updated until Refresh
- DS-1276 - [ECS] - CRM cannot retrieve activity for IAM users
- DS-1536 - Cyber Restore Manager - ERROR events showing up after CRM recovery and "lockout" jobs failing
- DS-1539 - [VAST]Query on root path is not returning any results
- DS-1540 - RWD - Cyber Recovery Manager - Parallel jobs with VAST failed due to unable to generate temporary s3 keys
- DS-1684 - Multi-platform support - API lockout support for Vast and Qumulo
- DS-1720 - [QUMULO] Lockout job tries to lockout access on an Export that was removed
- DS-1725 - [QUMULO] Restore job for NFS does not remove a row in Host Access that was added during lockout
- DS-1750 - [VAST] Vast is missing from the Action Event History lockout/restore lists
- DS-1753 - [ECS] RWD Ignored List/Monitor Only Settings - cannot add Path where the bucket name has an underscore
- DS-1874 - [Multiplatform][Isilon][Vast]NFS lockout behavior is not solid on multi platform
- DS-1891 - Converting an Ignore List to Monitor Only List removes duplicate IP address
- DS-1901 - Eyeglass Notification Center - no email received for ACCESS_RESTORED
- DS-2004 - [Multiplatform]Not all NFS Exports are locked out when using source IP in the Ignore List
- DS-2067 - [Multiplatform] Monitor state is not preserved when raising events from multiple platforms
- DS-2111 - RWD - Ignore List convert to Monitor Only Settings - Target NE Types and Network Elements not maintained for Vast & Qumulo
- DS-2122 - Bulk Ingest job getting stuck
- DS-2127 - [VAST, QUMULO] - rsw nfsevents state not respected
- DS-2131 - [Qumulo] Qumulo-only environment the SMB user displayed as SID
- DS-2126 - [VAST] hbase related services and containers are trying to start during cluster up for VAST only system
- DS-2144 - Webhooks data missing after offline upgrade
- DS-2166 - Easy Auditor - Finished Reports cannot load if RWS_ONLY_CFG=true
- Known Limitations
- DS-1702 - [POWERSCALE] - we do not reinstate the permission list order on restore
- DS-1892 - [ECS] RWD does not detect RSW event when user deletes more than one object at a time
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.8.3 (03/29/2024)
- Supported OneFS releases
- Supported Eyeglass releases
- Active Directory Compatibility
- End of Life Notifications
- Fixed in 2.9.0
- DS-892 NFS lockout/restore for multiple zones failing - Powerscale only.
- DS-893 Eyeglass is trying to lockout access on an Export that was removed.
- DS-130 Critical Snapshots are not created using the RWS Sera API
- RWD-547 ECS Ransomware Defender SecurityGuard uses port 9020 instead of 9021.
- New in Superna Eyeglass Ransomware Defender Edition Release 2.8.0 (03/01/2024)
- New in Superna Eyeglass Ransomware Defender Edition Release 2.6.4 (11/28/2023)
- Fixed in 2.6.4
- RWD-246 Files with non-ASCII characters fail to recover
- New in Superna Eyeglass Ransomware Defender Edition Release 2.6.3 (09/28/2023)
- Fixed in 2.6.3
- RWD-524 Webhook - missing share list for lockout alarm
- New in Superna Eyeglass Ransomware Defender Edition Release 2.6.2 (09/01/2023)
- New in 2.6.2-23282
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.6.1 (08/03/2023)
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.6.0 (06/29/2023)
- Fixed in 2.6.0
- RWD-279 Lockout API returns response code 500 for ECS IAM User
- RWD-365 ECS version 3.8 is now supported in Ransomware Defender for ECS and AirGap for ECS
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.12 (05/09/2023)
- Fixed in 2.5.12
- RWD-380 TD11 is not triggered as described in the documentation when using ECS
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.11 (04/03/2023)
- New in 2.5.11- 23110
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.10 (03/06/2023)
- Fixed in 2.5.10
- RWD-207 Files displayed after the hour-long wait
- RWD-192 Kafka topic empty after cluster down/up
- Support Removed in Eyeglass Release 2.5.9.1
- Deprecation Notices
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.9.1 (02/14/2023)
- Fixed in 2.5.9.1
- RWD-228 Syntax error in on-boot preventing proper startup timing.
- RWD-222 enable zkcleanup.timer by default
- RWD-145 [RWD-NFS Event] Major & critical events are locked out with default rule when reach threshold value even if - igls rsw nfsevents set --enabled=snapshotonly
- RWD-146 [RWD-NFS Event] Lockout option in Actions is also removed for SMB event when set igls rsw nfsevents set --enabled=snapshotonly
- RWD-113 Wrong Ransomware event state when created with POST /v2/ransomware/lockout/{user}
- RWD-114 Creating Critical Path Snapshots is blocked
- New in Superna Eyeglass Ransomware Defender Edition Release 2.5.9.1
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.9 (11/30/2022)
- Fixed in 2.5.9
- New in 2.5.8.1-22116
- Fixed in 2.5.8.1-22116
- Technical Advisory 31 - Ransomware Defender NFS Event Detection Always Enabled in 2.5.8.1-22080/22100
- New in 2.5.8.1-22100
- Fixed in 2.5.8.1-22100
- New in 2.5.8.1-22080
- T22197 Ransomware Defender Read-Only Role
- T22328 Ransomware Defender Event csv file storage
- T20285 Action menu for historical events now has option to restore access
- Fixed in 2.5.8.1-22080
- T21207 Custom Snapshot Expiry not preserved after modifying Settings on Threshold menu
- T21261 Cannot edit a user configured in the Ignored List or Monitor Only Settings
- New/Fixed in 2.5.8-22028
- New in 2.5.8-21330
- Fixed in 2.5.8-21330
- Security
- T22171 - Log4j Vulnerability - Upgrade to Log4j 2.17.0 (2.5.8-21330 and higher Log4j 2.17.0 )
- New in 2.5.8-21306
- Ransomware Defender Snapshot Management Enhancements
- T19619 Critical Path Snapshot
- T19823 Snapshot Budget
- T15666 New Behaviour Detections Enabled
- T21215 New SmartAirgap API
- NEW - OneFS 9.3 Support
- Fixed in 2.5.8-21306
- T22033 Log4j Vulnerability - CVE-2021-44228
- T11832 Ransomware Security Event which is promoted from Warning to Major does not respect Major Grace Period
- T18985 igls rsw restoreaccess cannot restore access for unresolvable user
- Technical Advisories
- Known Issues
- Threat Detection
- T4151 Action Window Event Action History does not show Unreachable Cluster
- T3732 Restored permission may be incorrect for consecutive lockouts
- T4081 Time Zone Mismatch between Ransomware Defender Security Guard Job History and Event History dates
- T22321 Escalation from major to critical will not change GUI status and lockout delay is blocked
- T4777 Snapshots not created for any Events that are Active when the Snapshot feature is enabled
- T4819 Empty Event History List
- T4950 Alarm text for failed Snapshot delete references Snapshot create
- T4955 Subsequent Create Snapshot action will delete reference to previously created snapshots if an error occurs during the create
- T5024 Major Events may reappear in the Active Events list after being recovered
- T5756 Error on restoring permissions does not raise an alarm
- T5954 Events that are promoted to Major due to multiple event “Upgrade to Major” are locked out immediately
- T6728 Extensions with special characters cannot be removed from the ignore list
- T7062 User may not be locked out in a multi-user security event
- T7190 Active Events may show State of Warning instead of Monitor when Monitor Mode is enabled
- T11586 NFS Lockout Event Information does not include NFS Export path
- T11590 NFS Lockout Event does not generate an PowerScale snapshot
- T14339 Restore Access Alarm must be manually cleared
- T15198, T15650 Ransomware Events may have inaccurate Signal Strength or may be reprocessed
- T15639 T18812 Error replicating AD Group or Local User Run as Root SMB permissions affects Lockout and Restore
- T16229 GUI incorrectly reports error when manually creating a snapshot
- T16462 NFS lockout may fail
- T18271 Ransomware Event State incorrect shows success when Powerscale is unreachable during restore operation
- T18643, T19217 State of Active Event shows WARNING when it should be MONITOR for File Filter in Monitor
- T18718 igls rsw allowed files remove option not working
- T18852 Ransomware Defender does not detect where path has square brackets [ ]
- T18887 Security Guard in Learned Thresholds prevents Security Guard job from detecting
- T18895 Ransomware Learned Threshold list doesn't open first time
- T19040 After upgrade to 2.5.7, Ransomware Events in Event History do not display the Signal Strength correctly
- T19106 Acknowledge/Archive options not blocked while lockout in progress
- T19198 Multiple concurrent Major Events not upgraded to Critical based on "Upgrade to Critical (events)" setting
- T19236 Honeypot file detector incorrectly crosses Major threshold in Monitor Mode
- T19356 Files/Folders with language characters not displayed properly in CSV and email
- T19409 Well known extension detection not working under some circumstances
- T20094 CLI command to restore access does not work when user name contains special characters
- T23012 Restore access for NFS lockout from Event History does not complete
- Security Guard
- T4197 Security Guard Error for Unlicensed Cluster
- T4228 Security Guard Temporary Errors
- T4965 Security Guard User Authentication Fails
- T15175 Existing Security Guard Logs lost formatting after upgrade to 2.5.6
- Manage Services
- T4192 Manage Services status not accurate after ECA Node Down
- General
- T4230 Blank Ransomware Defender Window
- T4183 Refresh does not work for Ransomware Defender multi-page lists
- T15457 HTML 5 vmware vcenter bug on OVA deployment
- T4336 Eyeglass Restore does not restore Security Guard Job History
- T4549 Ransomware Defender Settings Submit button enabled when no changes made
- T6617 PowerScale Directory Selector does not display hidden directories
- T18810 GUI not updated after cancelling an operation to switch modes
- T18660 Cannot use cloudapps URL to access Well Known Ransomware File Extension list
- T22450 Easy Auditor Event Rate alarm for Ransomware Defender Only deployments
- RWD-301 Error getting events - for NFS exports in Recovery Manager
- RWD-319 RSW events affected files are not presented in email
- RWD-362 Support ECS on RWD when turboaudit REST api is configured
- RWD-443 Easy auditor events only receiving and forwarding one signal and one file in file list despite of number of files and type of events
- RWD-535 Webhook - redundant lockout alarm when lockout/restore
- Features
- RWD-217 Event fails to upgrade with multiple user (ECS events only)
- RWD-85 zookeeper cleanup cron is not running as scheduled
- RWD-74 zookeeper cleanup cron is not running as scheduled
- DS-1536 Cyber Restore Manager - ERROR events showing up after CRM recovery and "lockout" jobs failing
- DS-1056 [ECS] CRM-Recovered count is not updated until Refresh
- DS-1276 [ECS] CRM-Cannot retrieve activity for IAM users
- DS-1051 [Powerscale] NFS lockout does not lockout the export without an IP added
- DS-1753 [ECS] RWD Ignored List/Monitor Only Settings - cannot add Path where the bucketname has an underscore
- RWD on-prem Release Notes
- Fixed in 2.9.0
- RWD-977 New UI - Security Guard alerts show as Critical in Alert Detail
- RWD-827 Critical path - Cannot add same path/user for different platforms
- RWD-909 Prevent Security Guard job to run in parallel on two devices
- Fixed in 2.8.2
- DS-198 New UI - SG history - sorted by time
- DS-190 Enhancement - Show the platform for Ignored list\Monitor only list
- DS-201 New UI - alerts window - SG filter is not working
- DS-203 New UI - Alerts overview details include HTML tags
- DS-204 New UI - SG log cannot be copied
- DS-213 New UI - Security Guard - running scan is reported as failed until completed successfully
- DS-214 New UI - Security Guard -information in the toast is not accurate
- DS-215 New UI - only successful Security Guard logs are presented
- DS-219 New UI - Events - Filter on user format domain\username fails
- DS-223 New UI - Recovery Manager - cannot filter by Cluster
- DS-222 New UI - events in error are not displayed
- DS-224 New UI - Logout returns a 403 Forbidden page
- DS-226 New UI - snapshots expiry/creation time is not correct on the new RWD UI
- DS-230 New UI - Alerts - SG events do not render unless you filter for them
- DS-232 Ignored List - NES not saved on Edit if Target NE Type is changed
- DS-233 New UI - No data available for policies/shares that are locked out
- Known Issues
- RWD-812 Ignored list/Monitor only list cross-platform behaviors are not consistent for users, paths, and client IPs
- RWD-865 New UI - More details for SG job
- RWD-730 SG runs Details should be grouped by cluster
- RWD-1026 CRM - fails to recover files with ‘&’ in filename (Vast, Qumulo)
- RWD-1042 Critical Snapshots are not created using the RWS Sera API
- RWD-1047 CRM Recovery Job reports the unrecovered file as Recovered
- DS-894 Missing Path Value.
- DS-857 Powerscale NFS lockout not working when using entire network/subnet.
- QUMULO release notes
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.8.3 for Qumulo (05/30/2024)
- Issue details
- Solution
- Fixed in 2.8.0
- QUMULO-86 User name is not displayed for NFS events
- QUMULO-87 SMB events cannot be marked as false positive
- Fixed in 2.8.2
- DS-157 SID is missing for users added in Learned Thresholds
- DS-158 Snapshot creation job is not starting on demand when all snapshot options are disabled
- DS-162 List for affected shares should be fixed for NFS RWD events
- DS-159 For NFS events after lockout/restore access, we are continuously adding rules
- DS-160 Recovery job is marked as failed, but files are recovered on the share
- DS-156 The NFS export with permission All is not locked out
- Qumulo Known Limitations
- DS-740 Additional host entry is not removed after restore user access on Qumulo NFS export
- Known Issues
- QUMULO-183 <user_name>@<AD_provider> user is not correctly handled in Ignore and Monitor lists
- QUMULO-289 Security Guard event is not changing state after restoring access
- QUMULO-275 Create SMB share for Security Guard
- QUMULO-326 Security Guard - support user format xxx@AD.test
- DS-970 [QUMULO] Monitor Only List- username field is case sensitive
- DS-1720 [QUMULO] Lockout job tries to lockout access on an Export that was removed.
- VAST Release Notes
- What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.8.3 for VAST (05/30/2024)
- Issue details
- Solution
- Fixed in 2.8.2
- DS-371 Manual snapshot fails if all options in Snapshot Settings are disabled
- DS-367 SG - igls-securityguard view should be created automatically
- DS-376 Easier to modify Vast SG access IP
- Known Issues
- VAST-161 Config rep Job fails if 2/more Views use the same View policy & Create Protected paths using those views
- VAST-287 RWD - Event detection for S3 for VAST is not supported
- VAST-364 All events duplicated in Recovery Mgr Event Details
- VAST-397 S3 views not replicating - no bucket owner
- VAST-399 Error replicating views inside a view
- DS-1224 [VAST] ad_principal_cache.json file is not populated correctly.
- DS-969 [VAST]: Monitor Only List- rsw events from added paths is received as warning/major/critical if path is entered in the format 'tenant:/path/to/object'
- DS-1540 [VAST] CRM- Parallel jobs with VAST failed due to unable to generate temporary s3 keys
- DS-1539 [VAST] Query on root path is not returning any results
- DS-1750 [Vast]Vast is missing from the Action Event History lockout/restore lists
- VAST Known Limitations
- Known Limitations
- Threat Detection
- T6914 Some extensions still result in lockout when added to the ignore list
- T15705 After upgrade to 2.5.6 cannot download CSV for Ransomware Event Files from events detected in prior releases
- T16723 Error on Lockout of Shares on DR cluster
- T17287 Many Access Zones slows down creation of snapshots and lockout
- T7574 Option to set learned threshold for Security Guard in RESTORED_USER_ACCESS state
- T18733 Ransomware Defender Affected Files Download Menu Naming
- General
- T16137 Anyrelease restore does not restore all Ransomware Defender and Easy Auditor settings
- T16821 anyrelease restore restrictions for restore to 2.5.7
- T20370 Monitor Only Settings Client IP applies to all PowerScale clusters
- T21852 RSW - Cannot configure and run SG after anyrelease backup and restore from an earlier build
- T21208 Snapshots taken using Action Menu for Ransomware Defender Event follow Ransomware / Snapshots settings
- T21110 Ransomware Defender / Snapshots User Share Snapshot Settings also applies for NFS detections
- Well Known Ransomware File Extension Whitelist management is not available when a proxy used
- T17624 Ransomware Defender NFS detection creates snapshot on SMB shares with Everyone permission
- RWD-75 Page-1 gets hide when navigate to Page-2 & archive all events from this page
- RWD-236 [RWD-NFS Event] User is displayed as "Root" or Sid ID instead of EXP:<client_ip>_<user_id>
- RWD-453 Only 100 affected files are listed in the webhooks event which triggers upon changing the state of RSW event
- DS-1243 [ECS] CRM-When a file is recovered we also recover the content
- DS-1357 [ECS] CRM does not restore "Owner" to recovered file
- DS-1360 [ECS] CRM cannot restore original file if "Read" is one of the permission
- DS-1702 [POWERSCALE] - Permission list order may not be reinstated upon restore
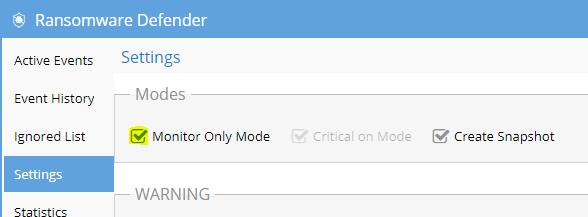
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.9.0
New in 2.9.0
Multiplatform Support:
Lockout/restore jobs will run for the event’s user on all configured platforms
Snapshot jobs will create snapshots for all accessible shares/exports across all configured platforms
User Normalization:
RWD events grouped by user (previously grouped by user+platform)
Event information is normalized to use a uniform format across platforms
ECS Support for Cyber Recovery Manager:
Recovery of ECS objects through Cyber Recovery Manager
Support for versioning
Noise Reductions for Paths
User can activate the learning mode to define the most common paths to whitelist
Will Perform the threshold analysis that will set a learned threshold for any event on this path
User will be prompted if there are more than X active events in Monitor mode
Usability Enhancements
- ECA - NTP settings pushed to other nodes
New UI Alerts handling and Recovery Manager Enhancements:
- User can provide feedback on their experience with the product.
- Improvements on the alerts lists and displaying cluster info.
- Recovery manager - add button to refresh snapshot cache
- Display labels on recovery status
- Add user alert history on the overview page.
- Monitor mode on the alerts list - display information when it expires
- SG - differentiate scans by Network Element
Fixed in 2.9.0
DS-892 NFS lockout/restore for multiple zones failing - Powerscale only.
NFS user lockout may fail with exports with the same export ID from different Powerscale clusters.
DS-893 Eyeglass is trying to lockout access on an Export that was removed.
Lockout job for NFS user may fail due to deleted NFS exports.
DS-130 Critical Snapshots are not created using the RWS Sera API
Critical Snapshots are not created using the RWS Sera API.
RWD-547 ECS Ransomware Defender SecurityGuard uses port 9020 instead of 9021.
ECS Ransomware Defender SecurityGuard uses port 9020 instead of 9021.
DS-125 Critical path - Cannot add same path/user for different platforms
It is possible to use the same user and paths for different platforms.
DS-126 Prevent Security Guard job to run in parallel on two devices
To avoid the situations in which users are locked out during job execution, the jobs parallelism is disabled.
DS-127 New UI - SG Alerts show as Critical in Alert Detail
On the Alerts page, new alerts will show their severity or if they are an alert raised by the Security Guard. If a Security Guard Alert is opened for more detail, it will show the true severity of that Alert.
DS-89 [Qumulo]Create SMB share for security guard
The SMBs for Security Guard are automatically created and their permissions are updated for Qumulo platform too.
Known Issues
DS-969 - [VAST]: Monitor Only List- rsw events from added paths is received as warning/major/critical if path is entered in the format 'tenant:/path/to/object'
Monitor Only List- rsw events from added paths is received as warning/major/critical if path is entered in the format 'tenant:/path/to/object'
DS-970 - [QUMULO]: Monitor Only List- username field is case sensitive
Monitor Only List- username field is case sensitive
DS-1051 - [Powerscale] NFS lockout does not lockout the export without an IP added
NFS lockout does not lockout the export without an IP added
DS-1056 - [ECS] CRM Recovered count is not updated until Refresh
Recovered count is not updated until Refresh
DS-1276 - [ECS] - CRM cannot retrieve activity for IAM users
Cannot retrieve activity for IAM users
DS-1536 - Cyber Restore Manager - ERROR events showing up after CRM recovery and "lockout" jobs failing
Cyber Restore Manager - ERROR events showing up after CRM recovery and "lockout" jobs failing
Workaround: get the user to manually add the eyeglass ip to the ignored list before running recovery jobs
DS-1539 - [VAST]Query on root path is not returning any results
Query on root path is not returning any results.
Workaround: Remove a "/" character when adding the root path
DS-1540 - RWD - Cyber Recovery Manager - Parallel jobs with VAST failed due to unable to generate temporary s3 keys
Parallel jobs with VAST failed due to unable to generate temporary s3 keys
DS-1684 - Multi-platform support - API lockout support for Vast and Qumulo
Lockout thought API doesn’t support Qumulo or Vast.
DS-1720 - [QUMULO] Lockout job tries to lockout access on an Export that was removed
[QUMULO] Lockout job tries to lockout access on an Export that was removed
DS-1725 - [QUMULO] Restore job for NFS does not remove a row in Host Access that was added during lockout
If a Qumulo NFS export is given read-access without IP specified and locked out, when the export is restored the host access rule that restricted access will not be removed.
DS-1750 - [VAST] Vast is missing from the Action Event History lockout/restore lists
Vast is missing from the Action Event History lockout/restore lists.
DS-1753 - [ECS] RWD Ignored List/Monitor Only Settings - cannot add Path where the bucket name has an underscore
[ECS] RWD Ignored List/Monitor Only Settings - cannot add Path where the bucket name has an underscore.
DS-1874 - [Multiplatform][Isilon][Vast]NFS lockout behavior is not solid on multi platform
Lockout jobs may be missing shares/exports if run quickly after restore job.
Workaround: Wait for replication job to run after restore before running a lockout job, or run the lockout job again after replication job if it seems shares/exports were not locked out.
DS-1891 - Converting an Ignore List to Monitor Only List removes duplicate IP address
If multiple network elements have configuration for the same IP address in the Ignored List, when the configuration is converted to Monitor Only List, only one network element will be retained.
Workaround: Before converting Ignored List, take note of which network elements are tied to multiple instances of an IP address. After converting to Monitor Only List, manually enter any missing entries into the list.
DS-1901 - Eyeglass Notification Center - no email received for ACCESS_RESTORED
Emails not being sent for ACCESS_RESTORED.
DS-2004 - [Multiplatform]Not all NFS Exports are locked out when using source IP in the Ignore List
If client IP is configured to be ignored for Vast in ignored list and another platform triggers an event from that IP, the Vast NFS exports will not be locked out during the multiplatform lockout process.
DS-2067 - [Multiplatform] Monitor state is not preserved when raising events from multiple platforms
If an event is raised with Monitor state due to monitor mode while multiplatform support is enabled, if more signals are raised on the same event from another platform on a path that is not in the monitor list, the event will be no longer be in Monitor state.
DS-2111 - RWD - Ignore List convert to Monitor Only Settings - Target NE Types and Network Elements not maintained for Vast & Qumulo
DS-2122 - Bulk Ingest job getting stuck
When running bulk ingestion the job seems to stuck at Wait for the Spark Job step. The job doesnt seem to finish.
Workaround: None available currently. User cannot ingest audit files from Isilon
DS-2127 - [VAST, QUMULO] - rsw nfsevents state not respected
Rsw nfsevents settings are not respected for Vast and Qumulo. If nfsevents is set to false Qumulo/Vast events will still be created, and if nfsevents is set to monitor the events will not have the correct state.
DS-2131 - [Qumulo] Qumulo-only environment the SMB user displayed as SID
Sometimes Qumulo only environment displays the SID instead of the userName.
Workaround: Restarting sca on eyelgass fixes the issue.
DS-2126 - [VAST] hbase related services and containers are trying to start during cluster up for VAST only system
Hbase related services and containers are trying to start during cluster up for VAST only system.
DS-2144 - Webhooks data missing after offline upgrade
Saved webhook data is not retained on upgrade.
Workaround: Copy the contents of /opt/superna/sca/data/eventWebhook.json file from Eyeglass. After updating, put the contents of this file back into the same location.
DS-2166 - Easy Auditor - Finished Reports cannot load if RWS_ONLY_CFG=true
Attempting to load finished EA reports while RWD_ONLY_CONF=true will result in an error and puts Eyeglass into a state that prevents pages from loading. Fixing this state requires restart of SCA.
Workaround: None
Known Limitations
DS-1702 - [POWERSCALE] - we do not reinstate the permission list order on restore
When we restore access to a PowerScale share (in case of user access across multiple users and shares), the permission type is restored but the order in which the user appeared in the Permission list is not restored to the state prior to lockout.
DS-1892 - [ECS] RWD does not detect RSW event when user deletes more than one object at a time
Ransomeware Defender does not raise events for ECS when multiple objects are deleted with a single action.
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.8.3 (03/29/2024)
Supported OneFS releases
8.2.0.x
8.2.1.x
8.2.2.x
9.0
9.1
9.2.x
9.3
9.4 via the February RUP 9.4.0.12 (PSP-3079) released Feb 8th 2023
9.4.0.14
9.5.x.x. (minimum version 9.5.0.1)
9.5.0.5
Supported Eyeglass releases
Superna Eyeglass Ransomware Defender Version | Superna Eyeglass Version |
| 2.6.3-23292 | 2.6.3-23292 |
| 2.6.2-23282 | 2.6.2-23282 |
| 2.6.1-23250 | 2.6.1-23250 |
| 2.6.0-23219 | 2.6.0-23219 |
| 2.5.12-23175 | 2.5.12-23175 |
| 2.5.11-23110 | 2.5.11-23110 |
| 2.5.8.1-22080 | 2.5.8.1-22080 |
| 2.5.8-22028 | 2.5.8-22028 |
| 2.5.8-21330 | 2.5.8-21330 |
| 2.5.8-21306 | 2.5.8-21306 |
| 2.5.7.1-21161 | 2.5.7.1-21161 |
| 2.5.7.1-21140 | 2.5.7.1-21140 |
| 2.5.7-21096 | 2.5.7-21096 |
| 2.5.7-21081 | 2.5.7-21081 |
| 2.5.7-21068 | 2.5.7-21068 |
| 2.5.6-20263 | 2.5.6-20263 |
Active Directory Compatibility
| Ransomware Defender Versions | Supported Active Directory Versions |
| 2.5.9, 2.5.8, 2.5.7, 2.5.6 all versions | Microsoft Active Directory 2012, 2016 |
Fixed in 2.9.0
DS-892 NFS lockout/restore for multiple zones failing - Powerscale only.
NFS user lockout may fail with exports with the same export ID from different Powerscale clusters.
DS-893 Eyeglass is trying to lockout access on an Export that was removed.
Lockout job for NFS user may fail due to deleted NFS exports.
DS-130 Critical Snapshots are not created using the RWS Sera API
Critical Snapshots are not created using the RWS Sera API.
RWD-547 ECS Ransomware Defender SecurityGuard uses port 9020 instead of 9021.
ECS Ransomware Defender SecurityGuard uses port 9020 instead of 9021.
New in Superna Eyeglass Ransomware Defender Edition Release 2.8.0 (03/01/2024)
New in Superna Eyeglass Ransomware Defender Edition Release 2.6.4 (11/28/2023)
Fixed in 2.6.4
RWD-246 Files with non-ASCII characters fail to recover
2.5.9-22231
Files with the extension modified to a known extension like .crypto will trigger TD7 events.
The original files are not recovered even if the Recovery Job finishes successfully.
New in Superna Eyeglass Ransomware Defender Edition Release 2.6.3 (09/28/2023)
Fixed in 2.6.3
RWD-524 Webhook - missing share list for lockout alarm
The lockout alarm in the webhook does not list shared information.
Workaround: None.
New in Superna Eyeglass Ransomware Defender Edition Release 2.6.2 (09/01/2023)
New in 2.6.2-23282
We'd like to highlight a specific update. The command ecactl cluster down now operates in the background mode by default. If you prefer the previous behaviour, you can still achieve it by running the command with the -serial option.What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.6.1 (08/03/2023)
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.6.0 (06/29/2023)
Fixed in 2.6.0
RWD-279 Lockout API returns response code 500 for ECS IAM User
Lockout API returns response code 500 for ECS IAM User
RWD-365 ECS version 3.8 is now supported in Ransomware Defender for ECS and AirGap for ECS
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.12 (05/09/2023)
Fixed in 2.5.12
RWD-380 TD11 is not triggered as described in the documentation when using ECS
TD11 is not triggered as described in the documentation when using ECS
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.11 (04/03/2023)
New in 2.5.11-23110
Zero Trust API now supports locking out ECS users.
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.10 (03/06/2023)
Fixed in 2.5.10
RWD-207 Files displayed after the hour-long wait
Tree View and All File Activity view will show content only after an hour-long wait.
RWD-192 Kafka topic empty after cluster down/up
kafka topic will reset after cluster down/up
Count and Size will reset to zero
- before cluster down/up
- after cluster down/up
Support Removed in Eyeglass Release 2.5.9.1
Deprecation Notices
No deprecation notices at this time.
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.9.1 (02/14/2023)
Fixed in 2.5.9.1
RWD-228 Syntax error in on-boot preventing proper startup timing.
Workaround: not necessary; verify startup has finished on other nodes, if applicable, before attempting to use the ECA.
RWD-222 enable zkcleanup.timer by default
As an ECA user, I don’t want to have to run systemctl enable --now zkcleanup.timer to start the service. This should be run by default on install/upgrade.
RWD-145 [RWD-NFS Event] Major & critical events are locked out with default rule when reach threshold value even if - igls rsw nfsevents set --enabled=snapshotonly
Major & critical events are locked out with default rule when reach threshold value even if -
igls rsw nfsevents set --enabled=snapshotonly
Steps-
1.Set igls rsw nfsevents set --enabled=snapshotonly in eyeglass
2.Raise NFS Event with Major/Critical severity ( Detector Mode -Enforcement)
3. Observe Locked out event with critical severity & Major event locked out after expiry
Expected Result -
It should not lockout nfs event even when we reach threshold value for Major & Critical events
RWD-146 [RWD-NFS Event] Lockout option in Actions is also removed for SMB event when set igls rsw nfsevents set --enabled=snapshotonly
Lockout option in Actions is also removed for SMB event when set igls rsw nfsevents set --enabled=snapshotonly
Workaround: you can set igls rsw nfsevents set --enabled=true/false/snapshotonly
RWD-113 Wrong Ransomware event state when created with POST /v2/ransomware/lockout/{user}
The Ransomware event that is created using POST /v2/ransomware/lockout/{user} API call has TO_LOCKOUT state. This event should be created with LOCKED_OUT state.
Workaround: manually run the lockout job from the actions menu on the event.
RWD-114 Creating Critical Path Snapshots is blocked
New in Superna Eyeglass Ransomware Defender Edition Release 2.5.9.1
zkcleanup.timer runs by default on install/upgrade
The NFS implementation to be more consistent with SMB processing
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.5.9 (11/30/2022)
Fixed in 2.5.9
Recovery Manager: Now included in ransomware defender is the ability to selectively view and recover all files that were affected by a ransomware event.
New in 2.5.8.1-22116
Refer to previous 2.5.8.1 builds.
Fixed in 2.5.8.1-22116
Technical Advisory 31 - Ransomware Defender NFS Event Detection Always Enabled in 2.5.8.1-22080/22100
Technical Advisory 31 is resolved in 2.5.8.1-22116.
New in 2.5.8.1-22100
Refer to previous 2.5.8.1 builds.
Fixed in 2.5.8.1-22100
Refer to previous 2.5.8.1 builds.
New in 2.5.8.1-22080
T22197 Ransomware Defender Read-Only Role
In the User Roles window there is a new option RANSOMWARE_READONLY to provide read only access to the Ransomware Defender window.
T22328 Ransomware Defender Event csv file storage
To improve disk space management on the operating system disk of the Eyeglass appliance, storage of the Ransomware Defender csv files used to store user event details has been moved to the larger disk used for storing larger application files such as log.
T20285 Action menu for historical events now has option to restore access
The Action menu for Ransomware Defender events in the Event History now has an option to Restore User Access.
Fixed in 2.5.8.1-22080
T21207 Custom Snapshot Expiry not preserved after modifying Settings on Threshold menu
A custom snapshot expiry set using the igls rsw generalsettings set --snapshot_expiry_hours command is reverted to the default value of 48 hours if there are any changes made and saved in the Ransomware Defender Threshold menu. No impact to snapshot creation, only the schedule is reverted to default.
Resolution: Custom snapshot expiry is now preserved.
T21261 Cannot edit a user configured in the Ignored List or Monitor Only Settings
Cannot edit entries for users configured in the Ignored List or Monitor Only Settings. The Save button has no action. Path and IP Address can be edited.
Resolution: User can now be edited in the Ignored List and Monitor Only Settings.
New/Fixed in 2.5.8-22028
Refer to previous 2.5.8 builds.
New in 2.5.8-21330
Refer to previous 2.5.8 builds.
Fixed in 2.5.8-21330
Security
T22171 - Log4j Vulnerability - Upgrade to Log4j 2.17.0 (2.5.8-21330 and higher Log4j 2.17.0 )
New in 2.5.8-21306
See What's New in Ransomware Defender here.
Ransomware Defender Snapshot Management Enhancements
The Ransomware Defender window has a new Snapshots menu where the new snapshot related features Snapshot Budget and Critical Path Snapshot will be managed. In addition, it is now possible to disable user share/export snapshots.
Documentation for Snapshot Management can be found here.
To maintain existing snapshot behaviour to take a snapshot at the base path of all shares that associated account has access to, ensure that the User Share Snapshot Settings “Enable Share Snapshots” checkbox is checked.
T19619 Critical Path Snapshot
Introduced in 2.5.8 one or more paths can be configured to always have a snapshot created for any detection.
T19823 Snapshot Budget
Going forward Ransomware Defender (2.5.8 build 21213 and higher) maximum number of snapshots created will be the configured Snapshot Budget (default is 5000). Prior to creating snapshots, Ransomware Defender will determine the number of Ransomware Defender specific snapshots (snapshot name starts with igls) and only if less than the snapshot budget will proceed with the snapshot step. If snapshots cannot be created due to snapshot budget a critical severity alarm is sent and the Event Action History is updated as well.
T15666 New Behaviour Detections Enabled
New behaviour detections are available and enabled by default.
IMPORTANT: This may introduce new detections that will need to be evaluated to determine whether additional tuning of Ransomware Defender settings is required. Recommend to enable Learning Mode after upgrade and verify no new events after several days. NOTE: Learning mode offers full file system protection.
T21215 New SmartAirgap API
New API is available that allows external applications to determine whether there are any active Ransomware Defender or Easy Auditor active events. More information can be found here.
NEW - OneFS 9.3 Support
Support for OneFS 9.3 is introduced in release 2.5.8.
Fixed in 2.5.8-21306
T22033 Log4j Vulnerability - CVE-2021-44228
Resolution: log4j version updated to 2.15.0 which has patch for the vulnerability.
T11832 Ransomware Security Event which is promoted from Warning to Major does not respect Major Grace Period
If a Ransomware Security Event is promoted from Warning to Major threshold, the associated user is locked out right away instead of starting Grace Period timer and only locking out if Grace Period has expired and no manual action has been taken. Note that a Ransomware Defender Security event which is raised at the Major level will respect the configured Grace Period.
Resolution: Major threshold Grace Period timer is now respected.
T18985 igls rsw restoreaccess cannot restore access for unresolvable user
If the user specified in the igls rsw restoreaccess cannot be resolved by the Access Zone AD provider. For example, a lockout might occur on shares provisioned with the Everyone permission even when the Access Zone AD provider cannot resolve the AD user.
Resolution: the igls rsw restoreaccess command can now be used to restore access for unresolvable user. Note that when using CLI to restore access the GUI is not updated with the new state.
Technical Advisories
Technical Advisories for all products are available here.
Known Issues
Threat Detection
T4151 Action Window Event Action History does not show Unreachable Cluster
In the event that a Cluster is unreachable during a Lockout operation, the Active Event state will correctly show ERROR and the Event Action History will show “Partially Locked out” but does not display the cluster that was unreachable or the shares that could not be locked out.
Workaround: Manually inspect the clusters that were locked out. Any missing cluster under management need to review the shares and determine which the affected user has access to and then manually block access.
T3732 Restored permission may be incorrect for consecutive lockouts
In the event that user share access has been locked and subsequently restored and another lockout occurs before Eyeglass inventory has run, the “restore” permissions associated with shares may be the lockout settings from the previous lockout.
Workaround: Permissions should be restored manually by removing the deny permission for the affected user. Use the Event Action History to determine the affected shares.
T4081 Time Zone Mismatch between Ransomware Defender Security Guard Job History and Event History dates
The Ransomware Defender Job History “Run Date” is based on the Eyeglass appliance time zone whereas the Event History “Detected” date is translated to the client browser locale.
Workaround: Translate date for 1 of the dates to the time zone of the other date to correlate Security Guard Jobs to events in the Event History.
T4151 Action Window Event Action History does not show Unreachable Cluster
In the event that a Cluster is unreachable during a Lockout operation, the Active Event state will correctly show ERROR and the Event Action History will show “Partially Locked out” but does not display the cluster that was unreachable or the shares that could not be locked out.
Workaround: Manually inspect the clusters that were locked out. Any missing cluster under management need to review the shares and determine which the affected user has access to and then manually block access.
T22321 Escalation from major to critical will not change GUI status and lockout delay is blocked
multi event escalation will block delayed lockout even if the UI shows delayed lockout.
Workaround: Change the multi event threshold to a higher value or make sure you do not leave many active events collect to avoid escalated response settings on the settings tab. These values should be increased if you plan to leave many active warning events without resolving them.
T4777 Snapshots not created for any Events that are Active when the Snapshot feature is enabled
If there are any Active Events when the Create Snapshot option is enabled, no Snapshots will be created for these already Active Events.
Workaround: Enable the Create Snapshot option when there are no Active Events. Events raised after the Create Snapshot option was enabled will have associated Snapshots created for affected shares.
T4819 Empty Event History List
There may be conditions where having other windows open such as the Event Action History may result in the Event History list being displayed with no entries.
Workaround: Close all Ransomware Defender related windows and then re-open the Ransomware Defender -> Event History tab.
T4950 Alarm text for failed Snapshot delete references Snapshot create
The alarm that is raised when a Snapshot delete fails contains the text “Failed to create snapshots” instead of “Failed to delete snapshots”.
Workaround: Check the Action Log for the event to determine whether a snapshot create or delete has failed.
T4955 Subsequent Create Snapshot action will delete reference to previously created snapshots if an error occurs during the create
The Create Snapshot action can be executed multiple times for a given event. If it has been run previously and then run again and the subsequent run has an error on creating any snapshot, the Snapshots list only contains the snapshots from the last run. Previously created snapshots are no longer displayed.
Workaround: Check the Event Action History log for complete list of created snapshots.
T5024 Major Events may reappear in the Active Events list after being recovered
An event which crosses the Major threshold and is recovered to Historical Events without being locked out (Stop lockout timer) may appear in the Active Events list again immediately after being recovered (Mark as recovered).
Workaround: Stop the lockout timer and Mark the event as recovered again. This may have to be repeated several times. Locking the affected user out followed by Restore User Access and then archiving the event as recovered may also resolve this issue.
T5756 Error on restoring permissions does not raise an alarm
If permissions restore action encounters an error there is no associated alarm notification.
Workaround: Review the Action History for the Event to confirm that all restores were successful.
T5954 Events that are promoted to Major due to multiple event “Upgrade to Major” are locked out immediately
For the case where there are multiple Warning events that cross the “Upgrade to Major” limit, when they are promoted to Major they are locked out right away instead of waiting for the configured Grace Period before locking out.
Workaround: The occurrence of this behaviour can be reduced by setting the “Upgrade to Major” threshold to a high number of users.
T6728 Extensions with special characters cannot be removed from the ignore list
Extensions have been added to the extension ignore list using the igls rsw allowedfiles add --extensions command cannot be removed from the ignore list using the igls rsw allowedfiles remove --extensions command.
Workaround: Contact Superna Support at support.superna.net to assist with removing these extensions.
T7062 User may not be locked out in a multi-user security event
It may occur that a user is only partially locked out when a multi-user lockout is occurring due to an error response from the PowerScale cluster during user resolution in Active Directory. In this case the error is not displayed in the Eyeglass event history.
Workaround: The Event History will contain the shares that were successfully locked out. Should events continue to be generated against the user for the unlocked share, it may be locked out a a result of subsequent event. User may also be locked out manually by adding the deny permission manually to share that was not locked out.
T7190 Active Events may show State of Warning instead of Monitor when Monitor Mode is enabled
Instead of the event state being Monitor in Active Events when Monitor Mode is enabled, the event state may incorrectly display as Warning instead.
Workaround: None Required. This is a display issue only. Verify that Monitor Mode is enabled on the Ransomware Defender / Settings tab.
T7525 Affected Files also shows Active Auditor Affected Files
When viewing the Affected Files for a Ransomware Defender security event, any files associated wtih an Active Auditor event that has occurred at the same time are also displayed.
Workaround: Download the csv file and use the path associated with the Ransomware Defender event from the GUI to filter the results.
T11586 NFS Lockout Event Information does not include NFS Export path
T11590 NFS Lockout Event does not generate an PowerScale snapshot
When a Ransomware Security Event is detected for an NFS client, the PowerScale snapshot against related paths is not created.
Workaround: Upgrade to release 2.5.8 and use critical path snapshot feature. PowerScale scheduled snapshots may also be available for recovery.
T14339 Restore Access Alarm must be manually cleared
A Restore Access alarm is generated when restoring access to user. Subsequent restore will not update an existing restore alarm or send a notification.
Workaround: After restoring access to user, in the Alarms window manually clear the alarm in order to receive notification on a subsequent restore.
T15198, T15650 Ransomware Events may have inaccurate Signal Strength or may be reprocessed
Ransomware Event processing may receive duplicate events and as a result may show a higher Signal Strength than is actually the case. The associated csv will also show duplicate entries for the same file. Ransomware processing may also intermittently skip a signal and as a result may show lower Signal Strength.
In some cases this may also result in a Ransomware Event being reprocessed at a later time.
Workaround: None required. The duplicate events result in early detection of Ransomware events. Skipping of signals is intermittent and subsequent signals cross threshold for detection.
T15639 T18812 Error replicating AD Group or Local User Run as Root SMB permissions affects Lockout and Restore
In some cases an SMB share permission that is configured with an AD groupor Local User that has Run as Root privileges has an error on share updates for Ransomware Defender that blocks Lockout such that it does not take effect or on Restore it does not restore the Run as Root SMB share permission.
Important: If you use run as root on shares you are exposing data to very high security risk since no ockout will be possible. This is because the user SID that is sent when an AD user accesses data with run as root enabled is the root user SID not the actual AD user SID.
We recommend to NOT use run as root on shares for the reason above and it fails all security audits of PowerScale in all industry standards (PCI, HIPPA, FedRAMP, ITSG, etc...). Remove run as root option on all shares.
Please review our documentation for more information: Securing root user on PowerScale.
Workaround: Manually restore or lockout user.
T16229 GUI incorrectly reports error when manually creating a snapshot
If you use the Action menu to manually create a snapshot, the GUI shows an error but the snapshot is actually created. Automatic snapshot creation as part of active event detection is not affected by this issue.
Workaround: None required as snapshot is created. Verify snapshot creation using Powerscale OneFS interface.
T16462 NFS lockout may fail
Under some conditions Ransomware Defender successfully detects security event and notifies regarding the event but the associated NFS lockout action fails.
Workaround: Manual steps to block access to the Powerscale cluster are required in this case.
T18271 Ransomware Event State incorrect shows success when Powerscale is unreachable during restore operation
If a Restore operation is initiated on an Active Event when the Powerscale cluster is unreachable, the restore steps will fail but the state of the Event on the Active Events GUI is ACCESS_RESTORED.
Workaround: None required. The Event Action History shows that the restore step failed. Once connectivity to the Powerscale cluster is restored the Restore operation can be retried.
T18643, T19217 State of Active Event shows WARNING when it should be MONITOR for File Filter in Monitor
When Ransomware Defender is configured for Enforcement Mode and Critical on Mode, an Active Event related to a File Filters extension in Monitor will be displayed in Active Events with State of WARNING instead of MONITOR.
No impact on behaviour, no lockout applied.
Impact to Automatic learning - the File Filter extension is not set to disabled.
Workaround: Review events and put File Filter extension into Disabled as required.
T18718 igls rsw allowed files remove option not working
The igls rsw allowed files CLI command executes and reports success but does not actually activate the extension or file entered in the command.
T18852 Ransomware Defender does not detect where path has square brackets [ ]
If path or file name on Powerscale cluster includes square Ransomware Defender encounters an error on processing and does not detect the security event.
Workaround: None available. Ransomware manipulation of other path/file continue to be monitored and acted upon.
T18887 Security Guard in Learned Thresholds prevents Security Guard job from detecting
If the Security Guard user is deleted from the Learned Threshold list it continues to be enforced and Security Guard events are not detected by Ransomware Defender. This will occur if Security Guard was in the Flag as False Positive list prior to upgrade to 2.5.7. In 2.5.7 Security Guard user cannot be added to the Learned Threshold list.
Workaround: Contact support.superna.net for assistance if after upgrade to 2.5.7 the Security Guard user needs to be removed from the Learned Threshold list.
T18895 Ransomware Learned Threshold list doesn't open first time
Under some conditions where name resolution proceeds slowly and/or Learned Threshold list contains may entries, list will not be displayed before 45s timeout occurs.
Workaround: Selecting the list a second time displays the list.
T19040 After upgrade to 2.5.7, Ransomware Events in Event History do not display the Signal Strength correctly
Signal strength not displayed correctly for Ransomware Events in the Event History after upgrade to 2.5.7 for events that were added to Event History in previous release.
Workaround: None required. These events had already been managed and archived on previous release.
T19106 Acknowledge/Archive options not blocked while lockout in progress
The Acknowledge / Archive options are incorrectly available to be used in the window of time between when the lockout action starts and the active event enters the Locked Out state. Impact: If selected during that window, the event never enters the Locked Out state and even though it is locked out and there for the restore option is not available to restore permissions.
Workaround: The Event Action History correctly documents the shares that were locked out and the account and time of lockout. The account can be restored from the command line following the instructions here for igls rsw restoreaccess command.
T19198 Multiple concurrent Major Events not upgraded to Critical based on "Upgrade to Critical (events)" setting
The setting to promote Active Events from Major to Critical without having to reach the Critical Threshold, "Upgrade to Critical (events) " is not respected. Events are not promoted until their Signal Strength Threshold crosses the Critical setting.
None Required: Events will be promoted if their Signal Strength Threshold crosses into Critical threshold and Lockout will be applied. For events that remain at Major severity if no manual steps taken, Lockout will be applied once grace period expires.
T19236 Honeypot file detector incorrectly crosses Major threshold in Monitor Mode
When Ransomware Defender has Monitor Mode active the Honeypot file detector incorrectly promotes a Honeypot event to Major instead of staying in Monitor state. Once promoted to Major the Grace Period timer begins and if no manual steps taken a lockout of the account will occur once the grace period expires.
Workaround: Upon notification of the Major event, manual steps can be taken from the Active Event Action menu to stop the Lockout timer and resolve the event from the GUI if appropriate. If a lockout occurs access can be restored through the GUI from the Active Event Action menu as well if appropriate.
T19356 Files/Folders with language characters not displayed properly in CSV and email
If the files/folders associated with a detected Ransomware security event contain language specific characters, the path/file names are not displayed correctly in the email sent as well as the CSV.
Workaround: Use the GUI to see the files and folders.
T19409 Well known extension detection not working under some circumstances
Under some circumstances when there have been no customization to the File Filters for well known extension detection, the well known vector for detection of Ransomware security event is skipped.
This does not affect the user behaviour or honeypot detection vectors.
Workaround: User behaviour and honeypot detection vectors still available for monitoring.
T20094 CLI command to restore access does not work when user name contains special characters
The igls rsw restoreaccess command does not execute if the user name contains special characters. Impact: No impact on lockout. Impact on ability to restore access.
Workaround: Use the Ransomware Defender Action Event history to identify all shares that were locked out and manually remove the deny permission using Powerscale native tools.
T23012 Restore access for NFS lockout from Event History does not complete
Using the Restore User Access option in the Event History for an unresolved NFS lockout will restore the permissions as expected but the job gets stuck at the Restore job initiated step and the overall status does not change to Recovered and no alarm is sent.
Workaround: Verify manually using OneFS native tools that client list for NFS export has been restored as expected.
Security Guard
T4197 Security Guard Error for Unlicensed Cluster
Security Guard fails when PowerScale Cluster selected to run is not licensed.
Since Ransomware Defender dynamically picks priority PowerScale Clusters to license (refer to Eyeglass Ransomware Defender Admin Guide for details on selection of licensed cluster) for the case where Eyeglass is managing more clusters than there are Ransomware Defender Agent Licenses, one cannot be sure the selected Cluster in Security Guard is actually licensed at the run time.
Workaround: Deploy same number of Ransomware Defender Agent Licenses as the number of PowerScale Clusters being managed by Eyeglass.
T8889 Cannot enable Security Guard with default schedule for on a newly deployed 2.5.3 ovf
The drop down list to schedule security has an invalid default.
Workaround: Click the drop down and set a valid schedule.
T4228 Security Guard Temporary Errors
Security Guard may occasionally error with 0 files written.
Workaround: This condition typically clears it self on the next Security Guard run. It does not affect workflow for a real security event.
If it does not clear, follow these steps to recover:
Archive as Unresolved
Run Security Guard manually to ensure that it is operational again.
T4965 Security Guard User Authentication Fails
When provisioning the Security Guard Active Directory User and password, Eyeglass checks that the username name and password entered can be successfully authenticated. It may occur on initial configuration that you will see the message “user could not be authenticated” even though the username and password are correct.
Workaround: After confirming that the username and password are correct, subsequent provisioning is successful.
T7574 Flag as False Positive Option should not be available for Security Guard Events
Security Guard provides automated end to end validation of Ransomware detection, lockout and restore and therefore should not be flagged as false positive. The Flag as False positive option is currently available to be selected for Security Guard events and should not be.
Workaround: Manual process required to prevent applying Flag as False positive to Security Guard events.
T15175 Existing Security Guard Logs lost formatting after upgrade to 2.5.6
Any existing Security Guard logs viewed from the Eyeglass GUI will have lost the formatting.
Workaround: None required. New logs will have the correct formatting.
Manage Services
T4192 Manage Services status not accurate after ECA Node Down
After an ECA node has been powered off / gone down and subsequently powered back on and rejoined to the ECA cluster it continues to display the Inactive state in the Eyeglass Manage Services window even when it is active again and healthy.
Workaround: Once the node is back up, remove it from the Manage Services window by selecting the X in the node’s row. Wait 1 to 2 minutes and the service should be rediscovered with the correct state.
General
T4230 Blank Ransomware Defender Window
After archiving an Event the Ransomware Defender window tabs may appear empty.
Workaround: Close and reopen the Ransomware Defender window.
T4183 Refresh does not work for Ransomware Defender multi-page lists
Ransomware Defender window with multiple pages is not updated by Refresh except for the first page.
Workaround: To update the list go back to the first page of the list.
T15457 HTML 5 vmware vcenter bug on OVA deployment
Some versions of vmware vcenter HTML user interface have a known issue with OVA properties being read correctly post power on, leading to first boot issues.
Workaround: use the Flash client as a work around.
T4336 Eyeglass Restore does not restore Security Guard Job History
Security Guard historical log files are not restored when you restore configuration from backup.
Workaround: None available.
T4549 Ransomware Defender Settings Submit button enabled when no changes made
When the Ransomware Defender Settings window is opened, the Submit button is enabled even though no changes have been made to any settings. If you navigate to another view and come back to Settings, the Submit button is then correctly disabled until a change is made on the page.
Workaround: None required.
T6617 PowerScale Directory Selector does not display hidden directories
Directories that start with a dot (.) are not displayed in the PowerScale Directory Selector.
Workaround: Use the PowerScale Directory Selector to enter \ifs\ and then enter the remainder of the path manually.
T8807 Deleting cluster from Eyeglass does not clear associated Ignore List and Wiretap settings
When an PowerScale cluster is deleted from management in Eyeglass, any associated Ransomware Defender Ignore List or Wiretap settings are not cleared.
Workaround: Manually delete Ignore List and Wiretap settings for deleted clusters.
T18810 GUI not updated after cancelling an operation to switch modes
In the Ransomware Defender Thresholds window, if you are switching between Advanced and Monitor or Advanced and Enforcement mode and upon being prompted you select No to cancel the operation, the GUI does not refresh and return to the original Advanced mode. Impact: Display issue only, the mode change is cancelled.
Workaround: Switch between tabs in the Ransomware Defender window or use the Eyeglass desktop Refresh Now button.
T18660 Cannot use cloudapps URL to access Well Known Ransomware File Extension list
The cloudapps URL documented here for accessing the Well Know Ransomware File Extension list does not resolve and returns a 404 response code.
Workaround: Following URL does resolve and can be used to manage the Well Known Ransomware File Extension list: https://storage.googleapis.com/rwdefender.superna.net
T22450 Easy Auditor Event Rate alarm for Ransomware Defender Only deployments
RWD-301 Error getting events - for NFS exports in Recovery Manager
Cyber Recovery manager will show error when trying to display the all activity files affected by NFS export events.
RWD-319 RSW events affected files are not presented in email
RSW events affected files are not presented in email
RWD-362 Support ECS on RWD when turboaudit REST api is configured
Support ECS on RWD when turboaudit REST api is configured
RWD-443 Easy auditor events only receiving and forwarding one signal and one file in file list despite of number of files and type of events
Easy auditor custom real time policy is only receiving and forwarding “one” signal for type create and delete despite of how many files are created or deleted.
RWD-535 Webhook - redundant lockout alarm when lockout/restore
Webhook - redundant lockout alarm when lockout/restore.
Features
RWD-217 Event fails to upgrade with multiple user (ECS events only)
RWD-85 zookeeper cleanup cron is not running as scheduled
TEST: zookeeper cleanup cron is not running as scheduled
Workaround:
1systemctl enable --now zkcleanup.timerRWD-74 zookeeper cleanup cron is not running as scheduled
zookeeper cleanup cron is not running as scheduledDS-1536 Cyber Restore Manager - ERROR events showing up after CRM recovery and "lockout" jobs failing
ERROR events showing up after CRM recovery and "lockout" jobs failing.
WORKAROUND: get the user to manually add the eyeglass ip to the ignored list before running recovery jobs
DS-1056 [ECS] CRM-Recovered count is not updated until Refresh
Recovered count is not updated until Refresh.
DS-1276 [ECS] CRM-Cannot retrieve activity for IAM users
Cannot retrieve activity for IAM users.
DS-1051 [Powerscale] NFS lockout does not lockout the export without an IP added
NFS lockout does not lockout the export without an IP added.
DS-1753 [ECS] RWD Ignored List/Monitor Only Settings - cannot add Path where the bucketname has an underscore
RWD Ignored List/Monitor Only Settings - cannot add Path where the bucketname has an underscore.
RWD on-prem Release Notes
Fixed in 2.9.0
RWD-977 New UI - Security Guard alerts show as Critical in Alert Detail
On the Alerts page, new alerts will show their severity or if they are an alert raised by the Security Guard. If a Security Guard Alert is opened for more detail, it will show the true severity of that Alert.
RWD-827 Critical path - Cannot add same path/user for different platforms
The identical critical path cannot be incorporated for the platforms.
RWD-909 Prevent Security Guard job to run in parallel on two devices
When the Security Guard is selected to run on two platforms, the Security Guard job is started in parallel. There is concurrency between the 2 Security Guard jobs to lockout the user, user is locked out by the Powerscale, and it fails to be locked out by the Qumulo Security Guard job.
Fixed in 2.8.2
DS-198 New UI - SG history - sorted by time
Security Guard sorting by time is not working correctly. The current Security Guard history is randomly sorted in the new UI.
DS-190 Enhancement - Show the platform for Ignored list\Monitor only list
The platform of Ignored list\Monitor only list is not displayed.
DS-201 New UI - alerts window - SG filter is not working
The Security Guard events are shown in the Security Guard category on the Alerts active window. When clicking on the Security Guard filter - no events are displayed.
DS-203 New UI - Alerts overview details include HTML tags
The HTML tags are displayed in the details for the Alert overviews.
DS-204 New UI - SG log cannot be copied
The Security Guard logs were shown to be copied, but they were not.
DS-213 New UI - Security Guard - running scan is reported as failed until completed successfully
The status in Last Scan for Security Guard shows as failed even though it is in progress. The scan is counted as failed.
DS-214 New UI - Security Guard -information in the toast is not accurate
Starting the Security Guard invokes a toast that suggests the run was completed, not that a run has started.
DS-215 New UI - only successful Security Guard logs are presented
Only successful Security Guard logs are displayed in the new UI.
DS-219 New UI - Events - Filter on user format domain\username fails
Filtering for users where the format is domain\firstname.lastname does not work. No values are returned.
DS-223 New UI - Recovery Manager - cannot filter by Cluster
There is no option to select for the Cluster filter. The user can filter by path.
DS-222 New UI - events in error are not displayed
Security Guard events only render if the user filters for them.
DS-224 New UI - Logout returns a 403 Forbidden page
Logout returns a 403 Forbidden page when you try to open 172.25.60.30/login
DS-226 New UI - snapshots expiry/creation time is not correct on the new RWD UI
Snapshot expiry and creation times are displayed incorrectly in the new RWD UI.
DS-230 New UI - Alerts - SG events do not render unless you filter for them
Security Guard events are only rendered if the user filters for them.
DS-232 Ignored List - NES not saved on Edit if Target NE Type is changed
When a user edits an Ignored Client IP entry, if they change the Target NE Type (e.g., from Vast to Qumulo), the value in the Source field and the Network Element checkbox does not persist. The user can enter a value in the Source field and check the Network Element, but the Network Element remains unchecked on Save.
Workaround: Remove the entry and re-add the new one
DS-233 New UI - No data available for policies/shares that are locked out
In the new UI, no additional data is available for policies/shares on triggered ransomware events that have been locked out.
Known Issues
RWD-812 Ignored list/Monitor only list cross-platform behaviors are not consistent for users, paths, and client IPs
The current ignored list/monitor-only list - Path/User entries only work for the corresponding platform cluster; Client IP works for all the platform clusters - behaviors are inconsistent.
RWD-865 New UI - More details for SG job
The Security Guard jobs page doesn’t include all the details regarding the job.
RWD-730 SG runs Details should be grouped by cluster
If the Security Guard job was enabled for more than one cluster, reviewing the logs is difficult.
RWD-1026 CRM - fails to recover files with ‘&’ in filename (Vast, Qumulo)
Files with ampersand in the filename cannot be recovered or are recovered incorrectly by CRM.
RWD-1042 Critical Snapshots are not created using the RWS Sera API
Critical snapshots are not created when SERA API is used even though the API status is successful.
RWD-1047 CRM Recovery Job reports the unrecovered file as Recovered
If a file is deleted after a snapshot was taken, CRM will not be able to recover it as it is not part of the recovery process. In addition, CRM incorrectly reports the file as “Recovered”.
DS-894 Missing Path Value.
The path value is missing in the shares list for NFS events.
DS-857 Powerscale NFS lockout not working when using entire network/subnet.
The lockout will fail when using network/subnet CIDR in the NFS permission field.
Workaround: Using individual IPs, e.g., from n.n.n.0/24 to n.n.n.n.
QUMULO release notes
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.8.3 for Qumulo (05/30/2024)
Issue details
We identified an inconsistency in the behavior of Ransomware Defender NFS lockouts. In certain cases, when an alert was triggered, lockout of SMB shares occurred, but the NFS lockout failed to execute. This issue did not affect the application's capability to detect and notify customers of an attack. Snapshots continued to be taken, and this issue did not impact the ability to recover any encrypted files.
Solution
We developed a patched version (2.8.3) that addressed this issue ensuring successful NFS lockouts. This issue is relevant only to customers with NFS lockouts enabled. If you do not use NFS lockouts, the upgrade is not immediately necessary. However, if you intend to begin using NFS lockouts, we recommend upgrading to version 2.8.3.
Fixed in 2.8.0
QUMULO-86 User name is not displayed for NFS events
When raising an NFS event generated by the root user, the user name displays 0 instead of root.
QUMULO-87 SMB events cannot be marked as false positive
The flag as false positive and learning mode functions for ransomware events generated by clients using the SMB protocol are not taking action.
Fixed in 2.8.2
DS-157 SID is missing for users added in Learned Thresholds
In the Learned Thresholds tab, user Security Identifiers (SIDs) are not shown for Threat Detectors instances flagged as false positives.
DS-158 Snapshot creation job is not starting on demand when all snapshot options are disabled
The snapshot creation job is not starting on demand when all snapshot options are disabled.
DS-162 List for affected shares should be fixed for NFS RWD events
The affected NFS exports are displayed correctly in the list, but there is a + sign to expand them next to them; there is nothing else to display.
DS-159 For NFS events after lockout/restore access, we are continuously adding rules
When a lockout or restore action is performed on an NFS event, a read-only rule is added to the NFS Export.
DS-160 Recovery job is marked as failed, but files are recovered on the share
The recovery job is marked as failed, but files are recovered on the share.
DS-156 The NFS export with permission All is not locked out
The NFS export with permission “All” is not able to be locked out.
Qumulo Known Limitations
DS-740 Additional host entry is not removed after restore user access on Qumulo NFS export
Additional host entry is not removed after restoring user access on Qumulo NFS export.
Known Issues
QUMULO-183 <user_name>@<AD_provider> user is not correctly handled in Ignore and Monitor lists
The following user format: <user_name>@<AD_provider> (ml1test@ad5.test) added to the Ignore or Monitor lists, is not handled correctly.
Users should use the following format: <AD_provider>\<user_name> (example: AD5/testuser) for Ignore or Monitor only lists.
QUMULO-289 Security Guard event is not changing state after restoring access
The Security Guard event remains in a lockout state after restoring access is done.
QUMULO-275 Create SMB share for Security Guard
Security Guard needs a dedicated SMB share to run its simulated attack. Currently, the user must manually create an SMB share for the Security Guard during the setup.
QUMULO-326 Security Guard - support user format xxx@AD.test
Only the user format AD\xxxx for the Security Guard is currently supported.
For user format xxx@AD.test is not currently handled.
DS-970 [QUMULO] Monitor Only List- username field is case sensitive
Monitor Only List- username field is case sensitive.
DS-1720 [QUMULO] Lockout job tries to lockout access on an Export that was removed.
[QUMULO] Lockout job tries to lockout access on an Export that was removed.
VAST Release Notes
What’s New in Superna Eyeglass Ransomware Defender Edition Release 2.8.3 for VAST (05/30/2024)
Issue details
We identified an inconsistency in the behavior of Ransomware Defender NFS lockouts. In certain cases, when an alert was triggered, lockout of SMB shares occurred, but the NFS lockout failed to execute. This issue did not affect the application's capability to detect and notify customers of an attack. Snapshots continued to be taken, and this issue did not impact the ability to recover any encrypted files.
Solution
We developed a patched version (2.8.3) that addressed this issue ensuring successful NFS lockouts. This issue is relevant only to customers with NFS lockouts enabled. If you do not use NFS lockouts, the upgrade is not immediately necessary. However, if you intend to begin using NFS lockouts, we recommend upgrading to version 2.8.3.
Fixed in 2.8.2
DS-371 Manual snapshot fails if all options in Snapshot Settings are disabled
Manual snapshot fails if all options in Snapshot Settings are disabled.
DS-367 SG - igls-securityguard view should be created automatically
Security Guard needs a dedicated SMB share to run its simulated attack. Currently, the user must manually create an SMB share for the Security Guard during the setup.
DS-376 Easier to modify Vast SG access IP
The IP for Security Guard cannot be altered directly.
Workaround: Choose a different entry, modify the IP, and then switch back to the desired entry.
Known Issues
VAST-161 Config rep Job fails if 2/more Views use the same View policy & Create Protected paths using those views
If we have two protected paths on the same tenant and a view under each path that uses the same view policy on the same tenant, AND each protected path replicates to a different tenant.
Workaround: set the view policy to use "ALL TENANTS" and rerun the config rep job.
VAST-287 RWD - Event detection for S3 for VAST is not supported
Ransomware Defender does not support detecting events from S3.
VAST-364 All events duplicated in Recovery Mgr Event Details
RENAME, CREATE, WRITE and DELETE events are duplicated in Event Details.
VAST-397 S3 views not replicating - no bucket owner
When the View is created on source with S3 protocol and bucket owner set. error occurs when replicating the target.
VAST-399 Error replicating views inside a view
When replicating views inside a view, the error occurs
The error:
DS-1224 [VAST] ad_principal_cache.json file is not populated correctly.
DS-969 [VAST]: Monitor Only List- rsw events from added paths is received as warning/major/critical if path is entered in the format 'tenant:/path/to/object'
Monitor Only List- rsw events from added paths is received as warning/major/critical if path is entered in the format 'tenant:/path/to/object'
DS-1540 [VAST] CRM- Parallel jobs with VAST failed due to unable to generate temporary s3 keys
Parallel jobs with VAST failed due to unable to generate temporary s3 keys
DS-1539 [VAST] Query on root path is not returning any results
Query on root path is not returning any results.
The workaround for this issue is when adding a root path is to remove one “/”.
DS-1750 [Vast]Vast is missing from the Action Event History lockout/restore lists
Vast is missing from the Action Event History lockout/restore lists.
VAST Known Limitations
Known Limitations
Threat Detection
T6914 Some extensions still result in lockout when added to the ignore list
For the following well-known extensions, a lockout will still occur even if these extensions have been added to the extension ignore list using the igls rsw allowedfiles add --extensions command:
*.[teroda@bigmir.net].masterteroda@bigmir.net
*.[mich78@usa.com]
*.symbiom_ransomware_locked
*.[resque@plague.desi].scarab
Workaround: Alternate Ignore capabilities for User, Path or IP address documented here may be used to workaround this issue.
T7191 SMB service not enabled when access restored when lockroot is true
If you have Ransomware Defender configured to disable SMB service is a root user event is detected (see Ransomware Admin guide here, section Securing Root User on PowerScale ), when you restore user access the SMB service is not automatically enabled.
Workaround: Manually enable SMB service on PowerScale once access is restored and you are ready to resume file access for SMB users.
T7670 Restoring user access via CLI does not update status of Security Event in the GUI
If you have restored user access after a lockout using the CLI command "igls rsw restoreaccess set --user=DOMAIN\\user ", the associated Security Event in the GUI will not be updated and remain in active state.
Workaround: Open the Actions window for the active event, enter a comment that access has been manually restored and then archive the event.
T8744 No event processing once Signal Strength passes 2 times Critical Threshold
For the case where both Ransomware Defender and Easy Auditor are licensed, reaching Signals processed count of 2 times Ransomware Critical threshold for a particular user limit is applied independently for Ransomware Defender and Easy Auditor.
Workaround: None Available.
T8986 NFS export lockout cannot be restored
Workaround: On lockout NFS clients are moved to "Always Read-Only Clients". They will need to be manually moved to the correct access type using Isilion GUI or CLI to modify the export.
T15705 After upgrade to 2.5.6 cannot download CSV for Ransomware Event Files from events detected in prior releases
After upgrading to Release 2.5.6, csv download of files related to Ransomware events generated on the previous release is not available.
Workaound: GUI can still be used to view the files or files may be found on the Eyeglass appliance in the /srv/www/htdocs/rsw_event_all_files directory.
T16723 Error on Lockout of Shares on DR cluster
Under some conditions where a Ransomware Defender Lockout job overlaps with a Configuration Replication job you may see an error locking out some shares on DR cluster with error message code 409 AEC_CONFLICT. No impact to protection from Ransomware as the shares on the DR cluster are providing access to read-only data.
Workaround: You can re-attempt the Lockout from the Ransomware Defender window Action menu for the Active Event. Deny permission can also manually from Powerscale interface as required.
T17287 Many Access Zones slows down creation of snapshots and lockout
In the case where there are many Access Zones configured, analysis of user accessible shares must be done for all Access Zones before snapshot processing or lockout is started.
Workaround: None available
T7574 Option to set learned threshold for Security Guard in RESTORED_USER_ACCESS state
The menu to add Security Guard to the Learned Threshold is incorrectly provided when the event is in the RESTORED_USER_ACCESS state. The option can be selected and indicates that the flag as false positive was applied but it is not actually applied and it does not appear in the Learned Threshold list.
Workaround: None required
T18733 Ransomware Defender Affected Files Download Menu Naming
The Ransomware Defender Affected Files Download Menu is incorrectly named Affected Files - All. As described in the Ransomware Defender documentation here it is possible to have more files associated with the event than displayed in the file.
General
T16137 Anyrelease restore does not restore all Ransomware Defender and Easy Auditor settings
There is no restore of settings from release 2.5.4 and earlier. For release 2.5.4 and earlier continue to capture all Ransomware settings (False Positive, Ignore List, Allowed Extensions, Security Guard) and Easy Auditor settings (Active Auditor Trigger settings, RoboAudit). Post restore verify settings and update where required before cluster up on ECA.
In all cases, restoring an Eyeglass backup using the --anyrelease option will not restore following Ransomware Defender and Easy Auditor settings:
Ransomware Defender: Event History, Threats Detected
Easy Auditor: Finished Reports, Scheduled Reports, Saved Queries
T16821 anyrelease restore restrictions for restore to 2.5.7
Ransomware Defender, Easy Auditor and Performance Auditor deployments cannot use the anyrelease restore option to upgrade to a new appliance running 2.5.7. For case where a backup & restore is required due to 42.3 OS on original deployment, a backup & restore to 2.5.6 will have to be done first followed by an upgrade to 2.5.7 or inplace OS upgrade prior to 2.5.7 upgrade.
T20370 Monitor Only Settings Client IP applies to all PowerScale clusters
If multiple Powerscale clusters are licensed for Ransomware Defender a setting in the Client IP list for Monitor Only Settings is applied to all clusters. There is no option to associate the setting to a specific cluster. Also if you convert Ignore List to Monitor list any Client IP setting from Ignore list will also be applied to all cluster.
T21852 RSW - Cannot configure and run SG after anyrelease backup and restore from an earlier build
After a backup and restore from the earlier release to Eyeglass 2.5.8, the Ransomware Defender window may no longer allow you to edit or run the Security Guard.
Workaround: After the restore, execute the 2.5.8 run file (same release as you restored to) to resolve the issue.
T21208 Snapshots taken using Action Menu for Ransomware Defender Event follow Ransomware / Snapshots settings
If the Enable Share Snapshots option in Ransomware / Snapshots is unchecked, selecting the Create Snapshot option from the Action Menu will also not create snapshots.
T21110 Ransomware Defender / Snapshots User Share Snapshot Settings also applies for NFS detections
The option to disable/enable Ransomware Defender snapshot functionality is called User Share Snapshot Settings and Enable Share Snapshots but applies to any Ransomware Defender detection for SMB or NFS.
Well Known Ransomware File Extension Whitelist management is not available when a proxy used
If a proxy has been configured to access the internet, the well-known ransomware file extension management does not account for the proxy and will not be able to resolve the configured URLs.
T17624 Ransomware Defender NFS detection creates snapshot on SMB shares with Everyone permission
A Ransomware Defender detection for operations over NFS protocol also creates snapshots for SMB shares that have the Everyone permission.
RWD-75 Page-1 gets hide when navigate to Page-2 & archive all events from this page
RWD-236 [RWD-NFS Event] User is displayed as "Root" or Sid ID instead of EXP:<client_ip>_<user_id>
When using nfs 4 version - it cannot show the EXP:<client_ip>_<user_id>
Workaround: use this command to mount the NFS export.
mount -o nfsvers=3 <isilon-ip>:<export-path> <mount-path>
RWD-453 Only 100 affected files are listed in the webhooks event which triggers upon changing the state of RSW event
Will not inherit number of files from original event.
DS-1243 [ECS] CRM-When a file is recovered we also recover the content
DS-1357 [ECS] CRM does not restore "Owner" to recovered file
DS-1360 [ECS] CRM cannot restore original file if "Read" is one of the permission
DS-1702 [POWERSCALE] - Permission list order may not be reinstated upon restore
In cases where multiple alerts are raised for users with access to overlapping shares, when restoring access to a PowerScale share, the permission type is restored, but the original order of users in the Permission list may not be restored to its state prior to the lockout.