Eyeglass Solutions Publication
SentinelOne Zero Trust Singularity Data Lake Integration
Home
What is SentinelOne?
- Overview
- Limitations
- Solution Overview
- Video Demo
- Advanced Zero Trust Capabilities
- What is SentinelOne?
- SentinelOne Marketplace
- Integration Architecture
- Solution Configuration in SentinelOne Singularity Data Lake and Security Edition Zero Trust
- Prerequisites
- Configuration in SentinelOne Singularity Data Lake
- Configuration Steps on Eyeglass Virtual Machine
- High Level steps
- Configuration Step by Step
- Configure the Service start and python integration files
- Configure the python packages and customize the SentinelOne Singularity Data Lake integration python code
- Configure Security Edition Zero Trust Webhooks
- How to test the Integration with SentinelOne Singularity Data Lake
- SentinelOne Singularity Data Lake SecOps administrators Integration Experience
Overview
Customers using SentinelOne Singularity Data Lake can now leverage a native integration that initiates native API integration to send root cause detections with details into natively parsed log entries within Singularity Data Lake by Superna Security Edition.
-
NOTE: This documentation is provided "as is" without support for 3rd party software. The level of support for this integration guide is best effort without any SLA on response time. No 3rd party product support can be provided by Superna directly. 3rd party components require support contracts
Limitations
- None
Solution Overview
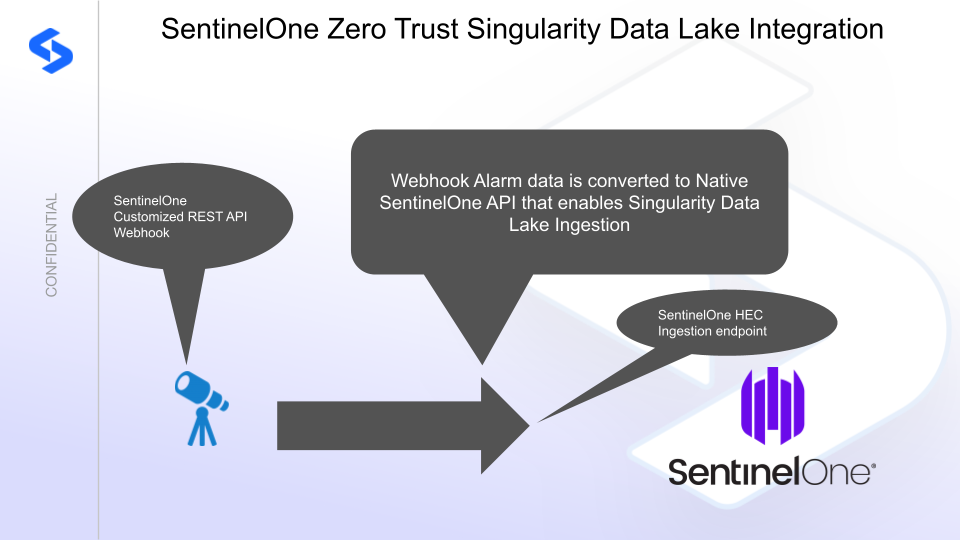
Superna Security Edition Zero Trust API receives webhook alerts from Security Edition and maps all relevant data fields into SentinelOne Singularity Data Lake.
Video Demo
Advanced Zero Trust Capabilities
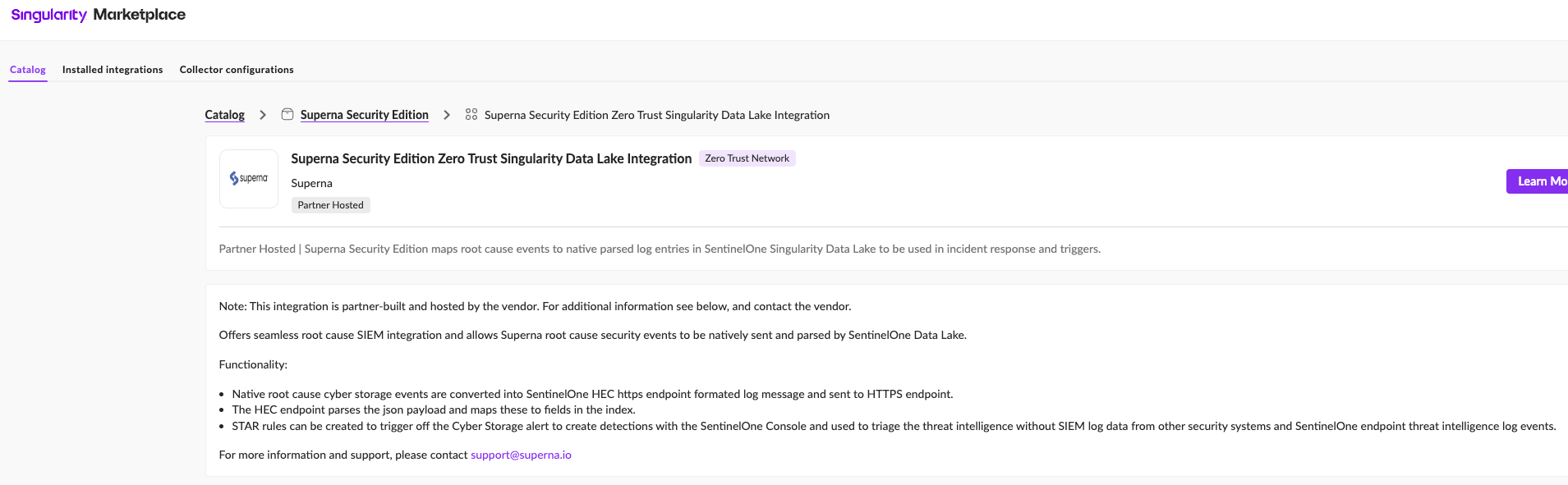
- Superna Security Edition maps root cause events to native parsed log entries in SentinelOne Singularity Data Lake to be used in incident response and triggers.
- Format of Zero Trust events are OCSF compliant.
What is SentinelOne?
SentinelOne is an Endpoint Detection and Response solution that employs artificial intelligence and machine learning to detect, prevent, and respond to cyber threats.
SentinelOne Marketplace
Integration Architecture
Solution Configuration in SentinelOne Singularity Data Lake and Security Edition Zero Trust
Prerequisites
- Installed Security Edition
- Eyeglass OS appliance version 15.5
- cat /etc/os-release
- License key for the Zero Trust API
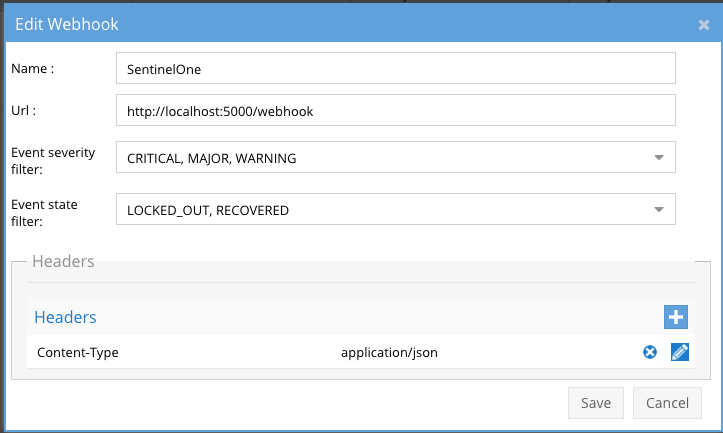
Configuration in SentinelOne Singularity Data Lake
To generate an API token in SentinelOne , you'll need to follow these steps.
- In policies & settings (left side menu) configure data ingest authentication by locating the Singularity Data Ingestion section.
- Then select Data ingestion
- Click on API keys tab
- Create a Log Access Key with Write access
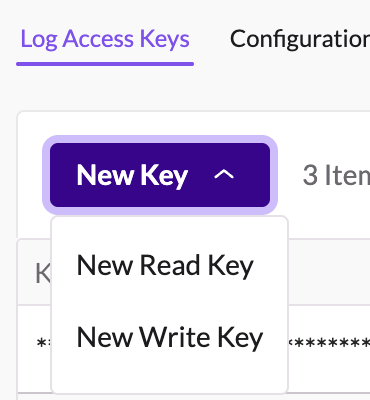
- Give the key a name example "Superna zero trust"
- Create a log write api key
- Record the api token to be used in the integration script.
Configuration Steps on Eyeglass Virtual Machine
High Level steps
- Create python location to run the application on the Eyeglass vm
- Create python main application script
- Create linux systemd service and set to auto start
- Create Zero Trust configuration in Security Edition
- Update the main script to customize with SentinelOne python code
- Test the script is running as a service
- Create a test event in Security Edition to validate the alerts appear as indexed parsed events in SentinelOne
Configuration Step by Step
Configure the Service start and python integration files
# SentinelOneSIEM Integration Deployment Instructions
Login to the Eyeglass VM via SSH as the admin user:
ssh admin@<your-vm-ip>
# Become root
sudo -s
mkdir -p /opt/superna/cgi-bin
chown -R sca:users /opt/superna/cgi-bin
chmod -R u+rwX,g+rwX /opt/superna/cgi-bin
# Switch to the SCA user
sudo -u sca -s
cd /opt/superna/cgi-bin
# Create Python virtual environment for the integration
python3 -m venv venv-sentinelonesiem
source venv-sentinelonesiem/bin/activate
# Install required Python packages
pip install flask boto3 requests logging
deactivate
# Create integration script files
touch sentinelonesiem.py
touch sentinelonesiem.sh
chmod +x sentinelonesiem.py
chmod +x sentinelonesiem.sh
# Create the sentinelonesiem.sh launch script
nano /opt/superna/cgi-bin/sentinelonesiem.sh
# Paste the following into the file:
#!/bin/bash
export PATH="/opt/.pyenv/bin:$PATH"
source /opt/superna/cgi-bin/venv-sentinelonesiem/bin/activate
exec python /opt/superna/cgi-bin/sentinelonesiem.py
# Make the script executable
chmod +x /opt/superna/cgi-bin/sentinelonesiem.sh
# Exit back to root
exit
whoami # confirm you are root
# Create the systemd service unit file
nano /etc/systemd/system/sentinelonesiem.service
# Paste the following into the file:
[Unit]
Description=Webhook listener for Zero Trust API translations and integrations
After=network.target
[Service]
Type=simple
User=sca
Group=users
WorkingDirectory=/opt/superna/cgi-bin
ExecStart=/bin/bash /opt/superna/cgi-bin/sentinelonesiem.sh
Restart=always
RestartSec=5
[Install]
WantedBy=multi-user.target
# Reload systemd to register the new service
systemctl daemon-reload
# Enable the service to start on boot (do NOT start it yet)
systemctl enable sentinelonesiem
Configure the python packages and customize the SentinelOne Singularity Data Lake integration python code
- Customize the application code by downloading the python code from this link to download
- Open the python template file in a text editor. NOTE: make sure to only replace the values and do not delete any of the commas
- Locate this section in the file # Replace with your SentinelOne HEC token and URL to add your SentinelOne api token and endpoint for API calls. Review this link on how to determine your ingestion URL.
- Add the API URL and API token into this section below
- # Replace with your SentinelOne HEC token and URLSENTINELONE_HEC_TOKEN = 'xxxxxxxxxx'SENTINELONE_HEC_URL = 'https://ingest.us1.sentinelone.net/services/collector/event'
- nano /opt/superna/cgi-bin/sentinelonesiem.py
- Open the file locally in Windows OS notepad and use control-A or select all the text in the python template
- Paste the clipboard into the ssh terminal session with the open nano editor file
- save the file
- press control+x
- Answer yes to save and exit the nano editor
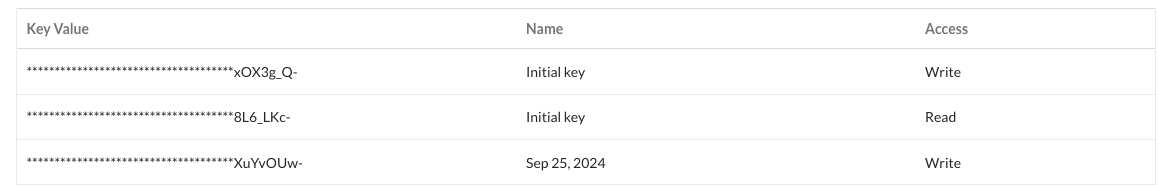
- Start the service and verify it is running
- systemctl start sentinelonesiem
- systemctl status -l sentinelonesiem
- Verify the service is started successfully and returns "active and running".
- If the service does not start do not proceed and double check the steps above are completed.
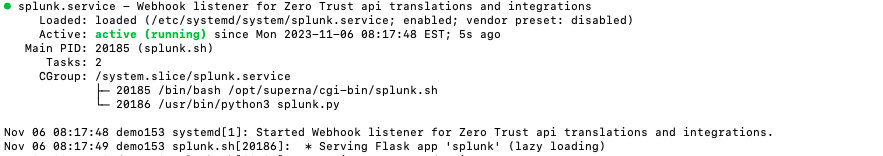
Configure Security Edition Zero Trust Webhooks
- The next step creates an Zero Trust Webhook URL.
- Configure Zero Trust endpoint in Ransomware Security Edition Zero Trust tab.
- Recommended Configuration: Only Critical and Major events and only the webhooks that set lockout or delayed lockout.Customers can customize based on specific requirements. The goal is to send findings versus a list of alarms that do not pinpoint a security incident.
- The endpoint url above will use localhost and will send Webhooks to the application service listening on port 5000. URL to use in the configuration
- http://localhost:5000/webhook
- Add the Content-Type header with value of application/json as shown above to complete the webhook configuration.
- Click save to commit the configuration.
- Click save on the main Webhook configuration page
- Configure Zero Trust endpoint in Ransomware Security Edition Zero Trust tab.
- Test the configuration is working following the next section
How to test the Integration with SentinelOne Singularity Data Lake
- Follow these steps to test the integration.
- Create a test lockout to generate a webhook,
- Create a banned file extension type in the Security Edition File Filter list
- Using a windows client pc mount an SMB share protected by Security Edition and create files with this section , create at least 100 files, verify your pc is locked out and an event is generated in the console.
- Now check SentinelOne console to verify if the network isolation network disconnect was processed.
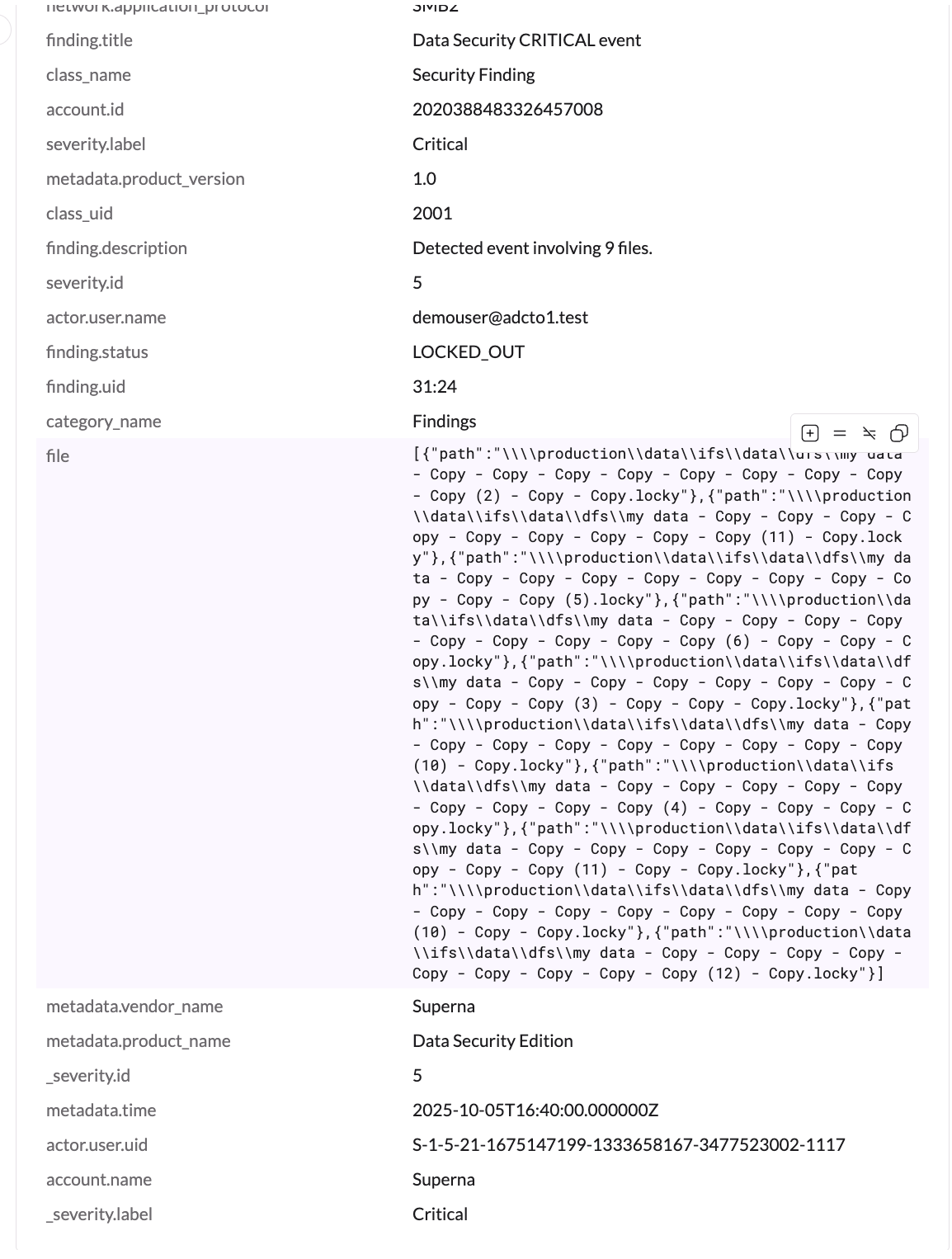
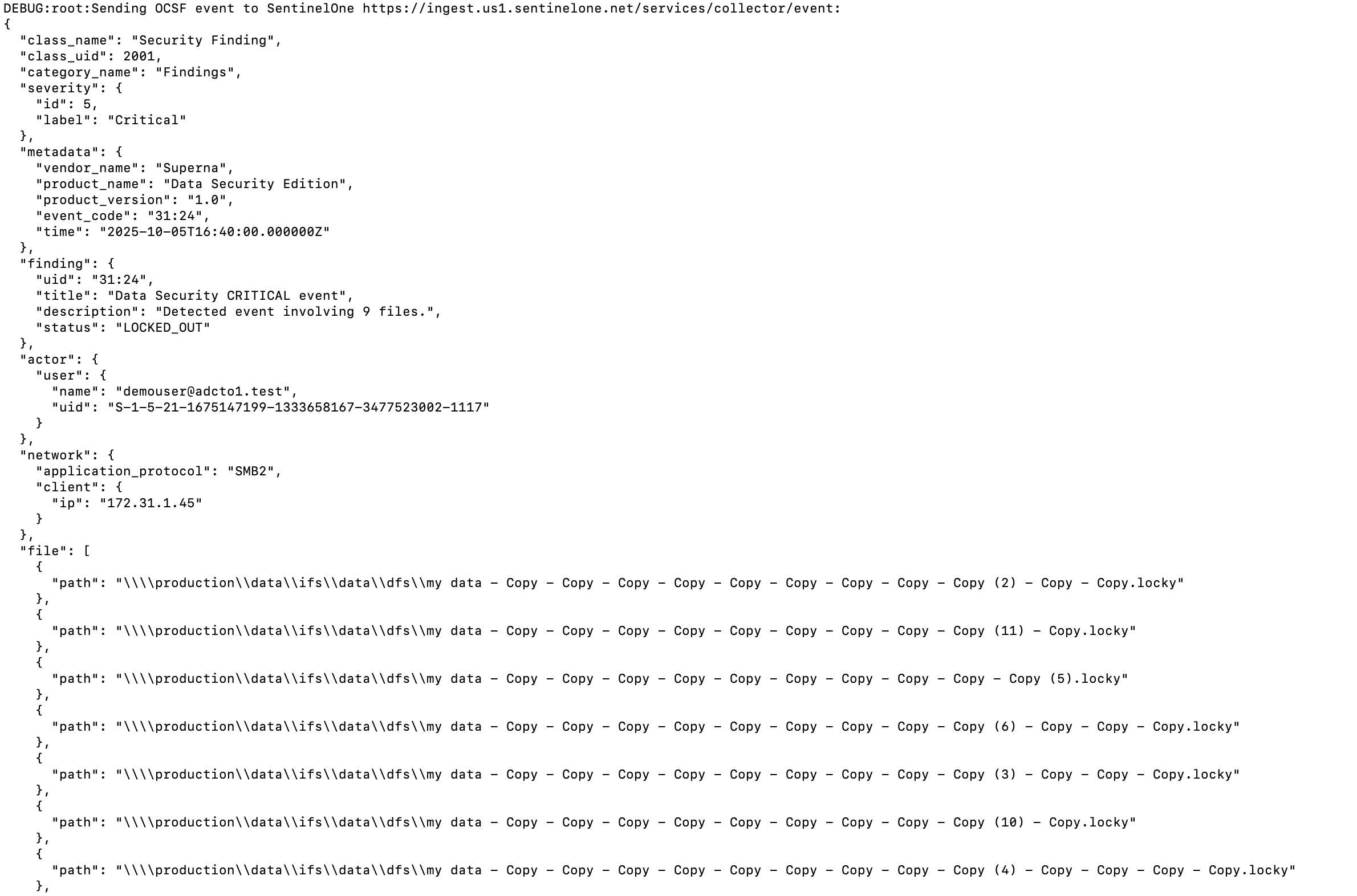
- See below what the user experience looks like in SentinelOne Singularity Data Lake console.
SentinelOne Singularity Data Lake SecOps administrators Integration Experience
Overview: Once configured, Superna Security Edition integration with SentinelOne enables real time alert ingestion using the integration code.
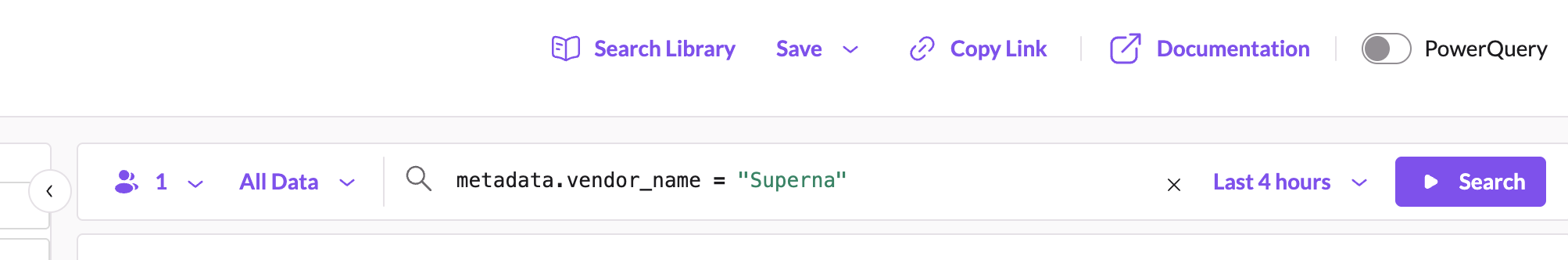
- Search for Superna events syntax: metadata.vendor_name = "Superna"