Logpresso SONAR SIEM Superna Zero Trust Alarm
- Overview
- Support Statement
- Limitations
- Solution Overview
- What is Logpresso Sonar SIEM?
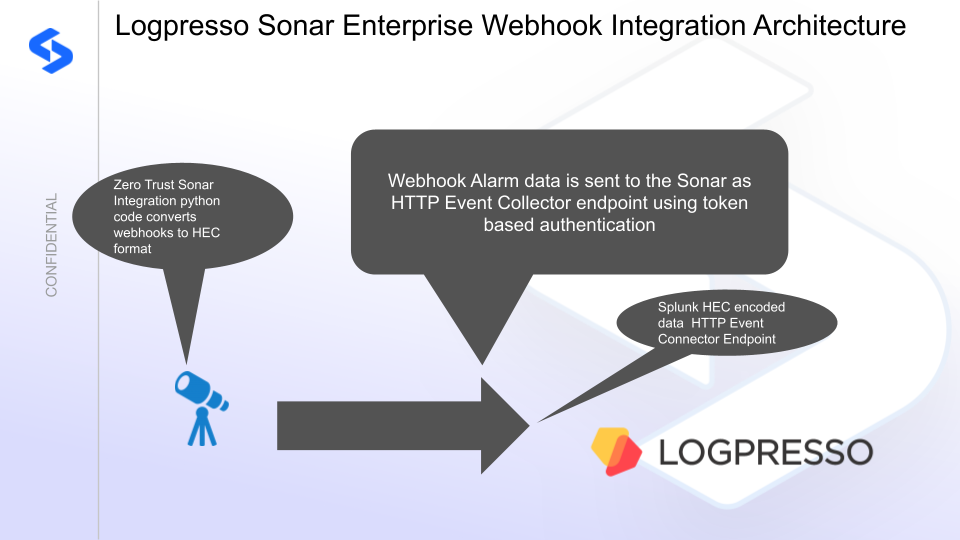
- Integration Architecture
- Solution Configuration in Logpresso Sonar SIEM and Defender Zero Trust
- Prerequisites
- Configuration in Logpresso Sonar SIEM
- Configuration Steps on Eyeglass Virtual Machine
- High Level steps
- Configuration Step by Step
- Configure the Service start and python integration files
- Configure the python packages and customize the LOGPRESSO integration python code
- Configure Defender Zero Trust Webhooks
- How to test the Integration with Logpresso Sonar SIEM
- Logpresso Sonar SIEM SecOps administrators Integration Experience
Overview
Customers using Logpresso Sonar SIEM can leverage this integration to send real time zero trust alerts using webhooks and maintain full payload parsing using json defined fields. The Splunk HTTP Event Connector capability within SONAR allows inbound webhook json payload to be parsed and tagged with a source type to allow for dashboards and triggers to be leveraged in workflows.
Support Statement
-
NOTE: This documentation is provided "as is" without support for 3rd party software. The level of support for this integration guide is best effort without any SLA on response time. No 3rd party product support can be provided by Superna directly. 3rd party components require support contracts
Limitations
- HTTPS with un-signed certificates is the default configuration and certificate checking has been disabled in this sample code.
Solution Overview
Superna Data Security Edition Zero Trust API is the cornerstone technology used to integrate with SIEM, SOAR and XDR platforms. Automation begins with data that summarizes the threat and places that information into a security tools to be acted on by Secops and run playbooks to protect corporate IT assets from vulnerabilities and insider or external attackers.
What is Logpresso Sonar SIEM?
Integration Architecture
Solution Configuration in Logpresso Sonar SIEM and Defender Zero Trust
Prerequisites
- Installed Data Security Edition subscription product
- Eyeglass OS appliance version 15.5
- cat /etc/os-release
- License key for the Zero Trust API
- Logpresso Sonar and Logpresso Maestro
- HEC endpoint URL and token value
- endpoint replace xxxxx with your instance name url. https://xxxxxx.logpresso.
cloud/services/collector - Logpresso Sonar Integration page.
- Schema - https://logpresso.store/en/apps/superna-data-security/log-schemas/superna-zt-alarm
Configuration in Logpresso Sonar SIEM
- Steps to Configure Logpresso Sonar
- Install the Splunk app application into the SONAR instance
- Set the API token
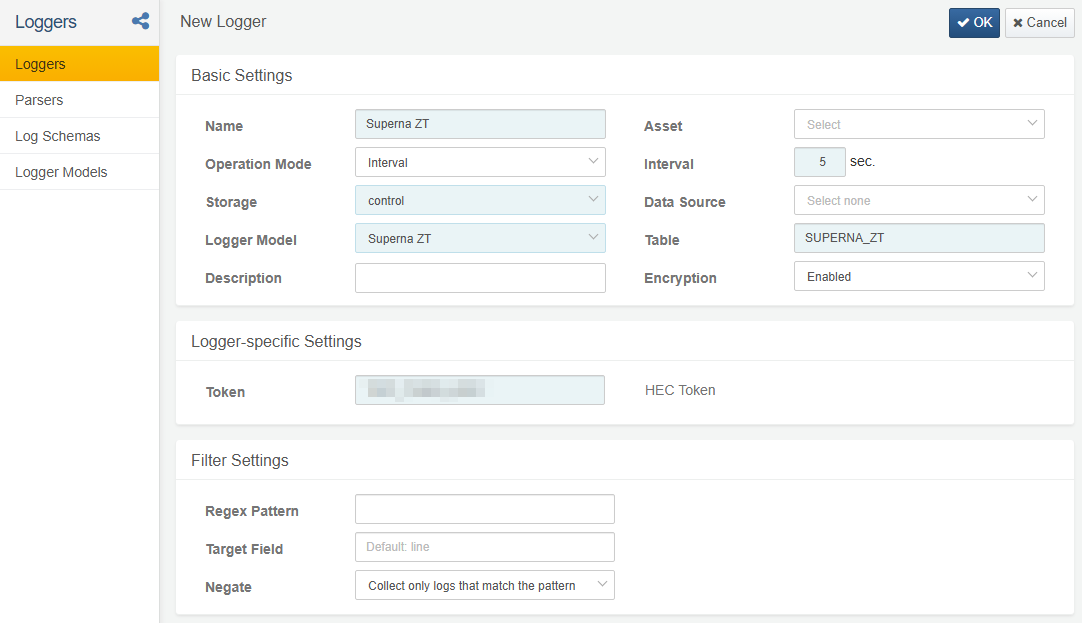
- record the token value
Configuration Steps on Eyeglass Virtual Machine
High Level steps
- Create python location to run the application on the Eyeglass vm
- Create python main application script
- Create linux systemd service and set to auto start
- Create Zero Trust configuration in Defender
- Update the main script to customize with Logpresso Sonar SIEM python code
- Test the script is running as a service
- Create a test event in Defender to validate the alerts appear as indexed parsed events in Logpresso Sonar SIEM
Configuration Step by Step
- Login to the eyeglass VM as admin user
- Follow the steps below
Configure the Service start and python integration files
Configure the python packages and customize the LOGPRESSO integration python code
- Customize the application code by downloading the python code from this link to download
- Open the python template file in a text editor. NOTE: make sure to only replace the values and do not delete any of the commas
- Locate this section in the file
- LOGPRESSO_HEC_TOKEN = 'xxxxxxxxxxxxxxxx'
- LOGPRESSO_HEC_URL = 'https://yyyyyyyyyyyyyy/services/collector'
- Replace the xxxxx with the HEC token recorded from the steps above and replace yyyy with the IP address of the sonar server running the HTTP Event Collector
- Paste the updated script into the production file
- nano /opt/superna/cgi-bin/logpresso.py
- Open the file locally in Windows OS notepad and use control-A or select all the text.
- Paste the clipboard into the ssh terminal session with the open nano editor file
- save the file
- press control+x
- Answer yes to save and exit the nano editor
- Start the service and verify it is running
- systemctl start sonar
- systemctl status -l logpresso
- Verify the service is started successfully and returns "active and running".
- If the service does not start do not proceed and double check the steps above are completed.
Configure Defender Zero Trust Webhooks
- The next step creates an Zero Trust Webhook URL.
- Configure Zero Trust endpoint in Ransomware Defender Zero Trust tab.
- Recommended Configuration: Only Critical and Major events and only the webhooks that set lockout or delayed lockout. Customers can customize based on specific requirements. The goal is to send findings versus a list of alarms that do not pinpoint a security incident.
-
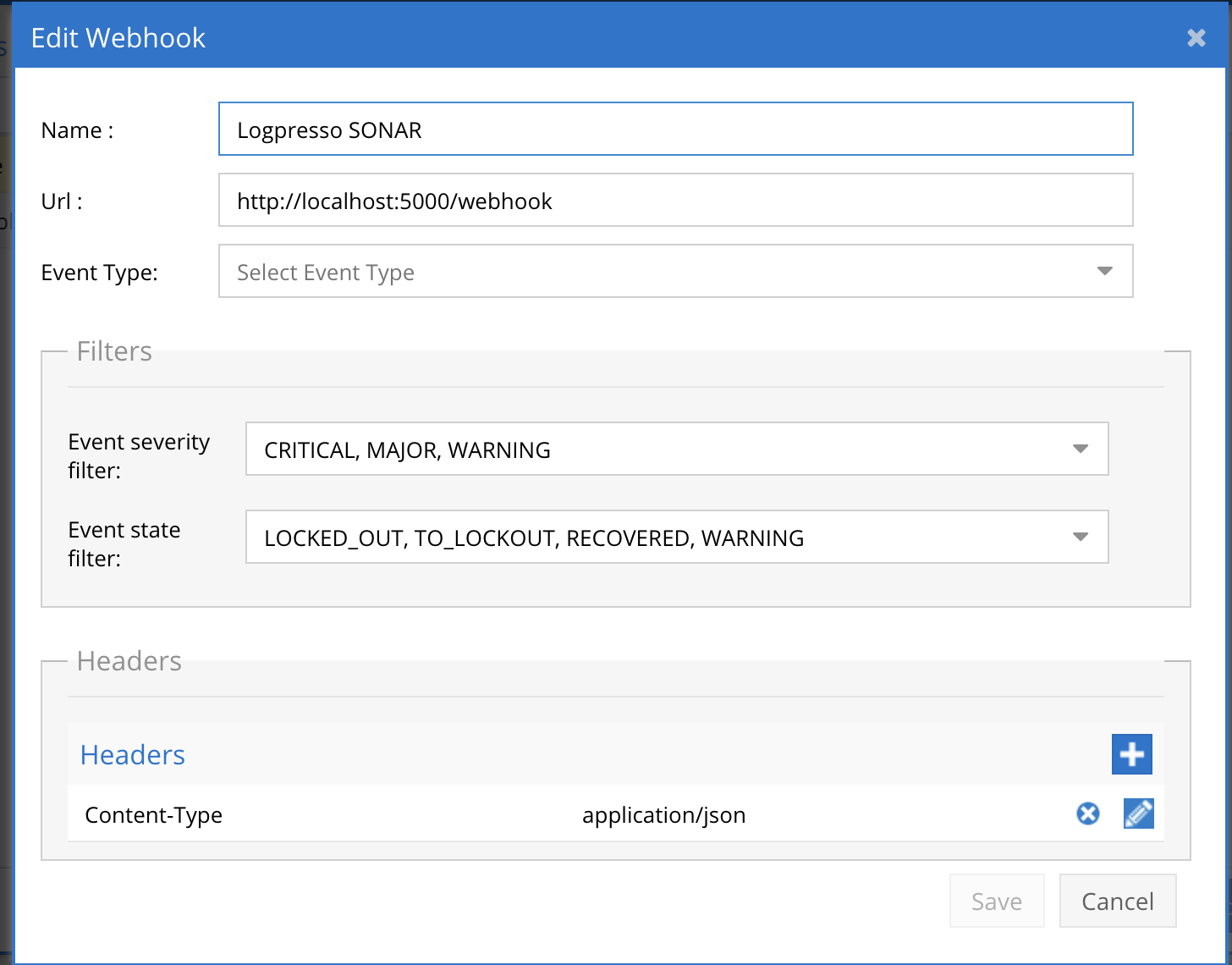
- The endpoint url above will use localhost and will send Webhooks to the application service listening on port 5000. URL to use in the configuration
- http://localhost:5000/webhook
- Add the Content-Type header with value of application/json as shown above to complete the webhook configuration.
- Click save to commit the configuration.
- Click save on the main Webhook configuration page
- Configure Zero Trust endpoint in Ransomware Defender Zero Trust tab.
- Test the configuration is working following the next section
How to test the Integration with Logpresso Sonar SIEM
- To test the integration follow these steps
- download this curl command template and open with a text editor
- Copy all the text
- ssh to the eyeglass vm as the admin user
- paste the entire cli command to the ssh prompt to send sample data to the running Zero Trust application. This will send test data directly to the application to be processed and sent to Logpresso logpresso SIEM.
- The output of a successfully processed webhook test will return this text in the ssh terminal
- done sending event to logpresso and check for http 200 and success count in response
- How to review the process logs from the web application
- sudo -s
- journalctl -f -u splunk
- This allows you to view the logs generated by the application.
- To log to a file and review with nano showing only the most recent 250 lines.
- journalctl -f -n 250 -u logpresso > /tmp/ztwebhook.log
- nano /tmp/logpresso.log
- In the log below the response code from the Logpresso Sonar SIEM api call should show http 200 status code and successCount 1 to indicate the Finding was successfully created.
- You can also view logpresso.log for specific error messages.
- Go to the Logpresso Query menu and run table SUPERNA_ZT to check the results.
- Done
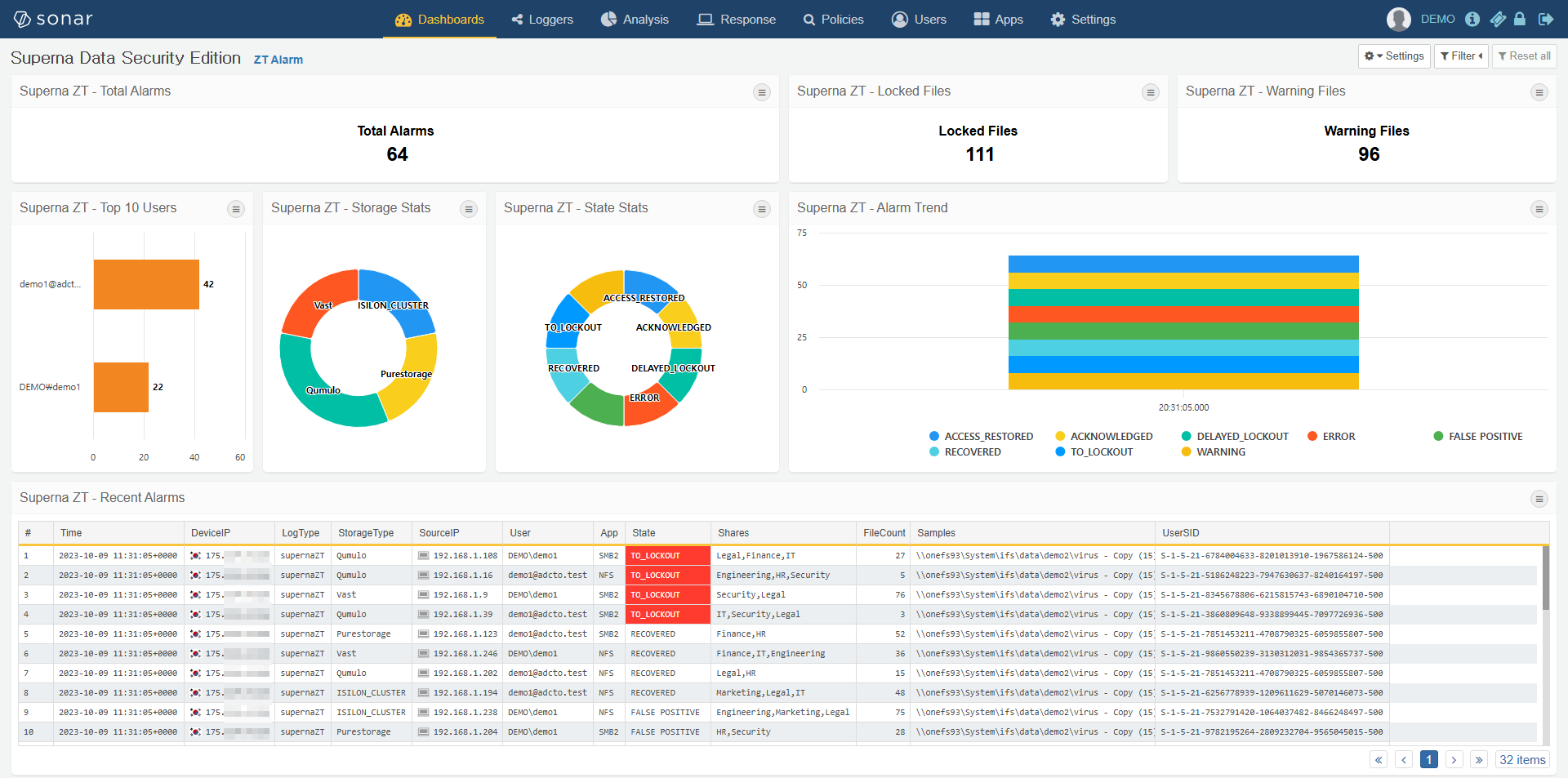
Logpresso Sonar SIEM SecOps administrators Integration Experience
- Once the integration has been tested, it is possible to build triggers from indexed parsed zero trust fields.