- Security Event Column Definitions
- Shares and Snapshots columns in Ransomware Active Events
- Files and CSV Download Column Ransomware Active Events
- Threat Detection Signal Strengths in Ransomware Active Events
- Signal Strength Window In Ransomware Active Events
Security Event Column Definitions
- File Event: a discrete event published by PowerScale’s event stream based on a user action, for example: open file, close file, write or read to file.
- User: The user or NFS IP of the locked out account
- Shares : List of shares that were locked out
- Snapshots: List of snapshots of SMB share paths taken during the lockout
- Threat Detectors: Logic used by Eyeglass Ransomware Defender to determine if a group of File Events is potentially associated with a Ransomware attack. There are multiple independent threat detectors used by Eyeglass Ransomware Defender during analysis that are assessed in parallel.
- Signal: Occurrence of one or more File Events that have been flagged by one or more threat detectors as a potential Ransomware Event.
- Signal Strength: For a given Signal, the number of threat detectors that were triggered. A higher Signal Strength has a higher probability of being a Ransomware Event.
- Ransomware Event: A collection of signals whose combined Signal Strengths exceeds the user-set threshold in Eyeglass.
- Files: The list of files associated to the detection for the specified user.
- Lock Out: The date and time of the security event
- Client IP: The ip address of the users PC that is infected.
- Actions: The history of all steps taken during the detection is listed with time stamps. All share lockout or snapshot create tracking is logged along with any failed API calls to lockout or create snapshots. All future actions stay with the event history, example restore user, comments, flag as false positive etc... If an event is archived the history will stay with the event in the Event History tab.
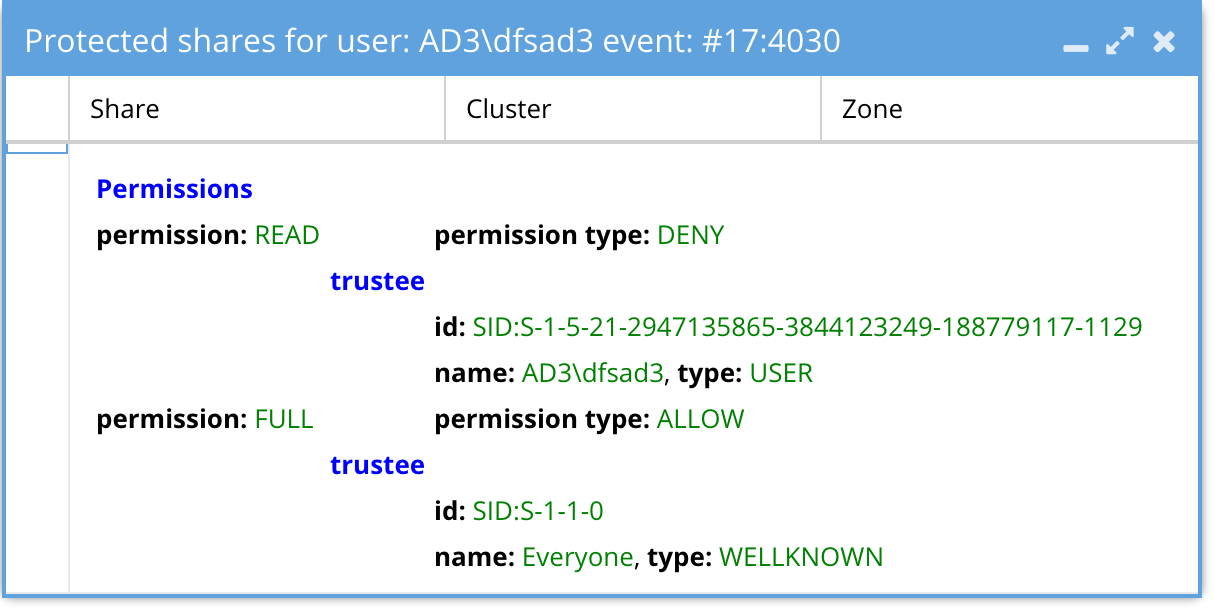
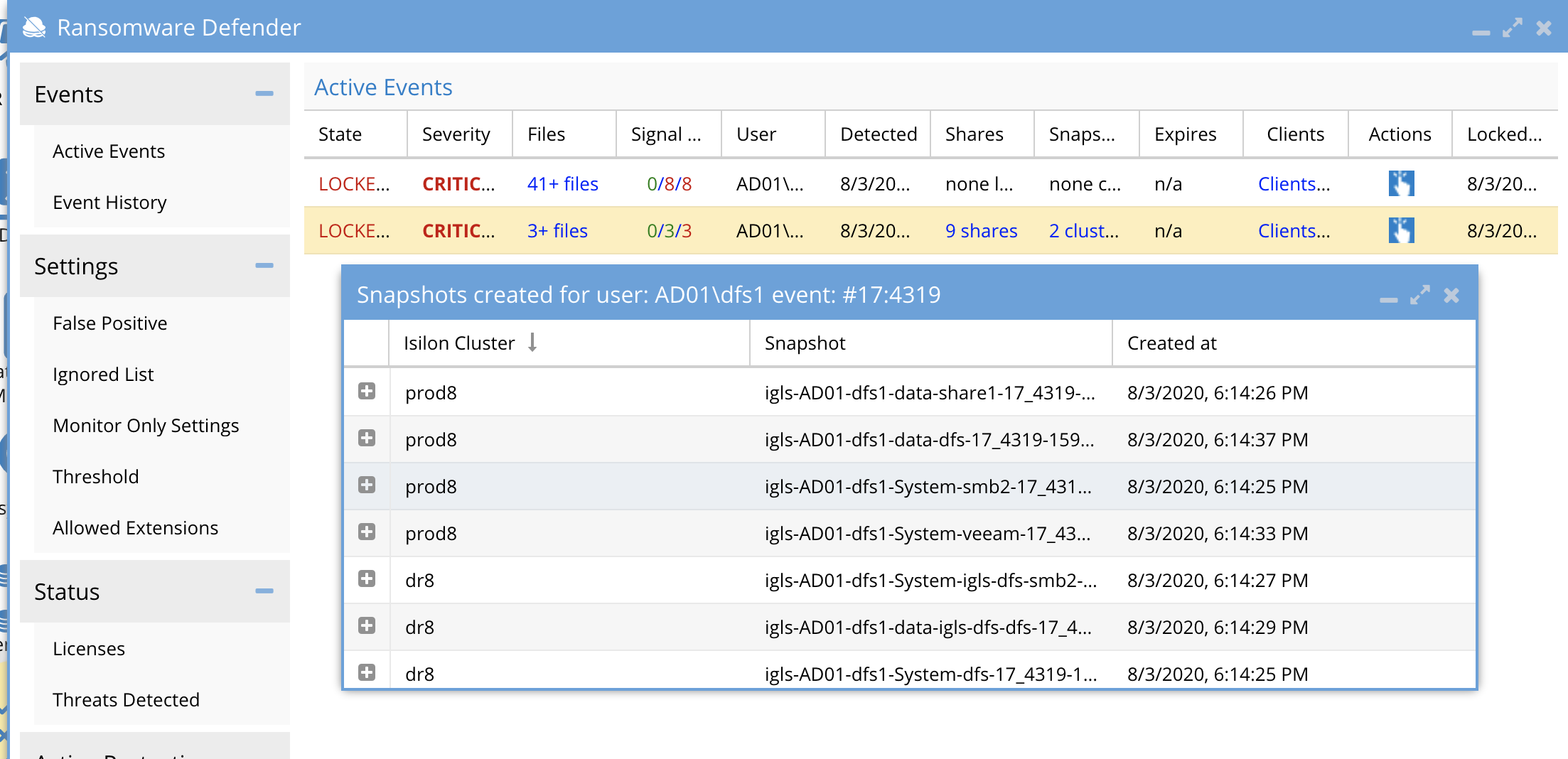
Shares and Snapshots columns in Ransomware Active Events
- The shares column lists shares that were locked out for this specific user listed in the User column. The shares are detected based on AD group membership of the detected user and locks out on all shares on all clusters managed by the Eyeglass.
- The snapshots column lists the snapshots that we triggered during the lockout. The snapshots are taken on the SMB share paths of all shares on all clusters as detected as accessible to the user. The snapshots default with an expiry of 48 hours.
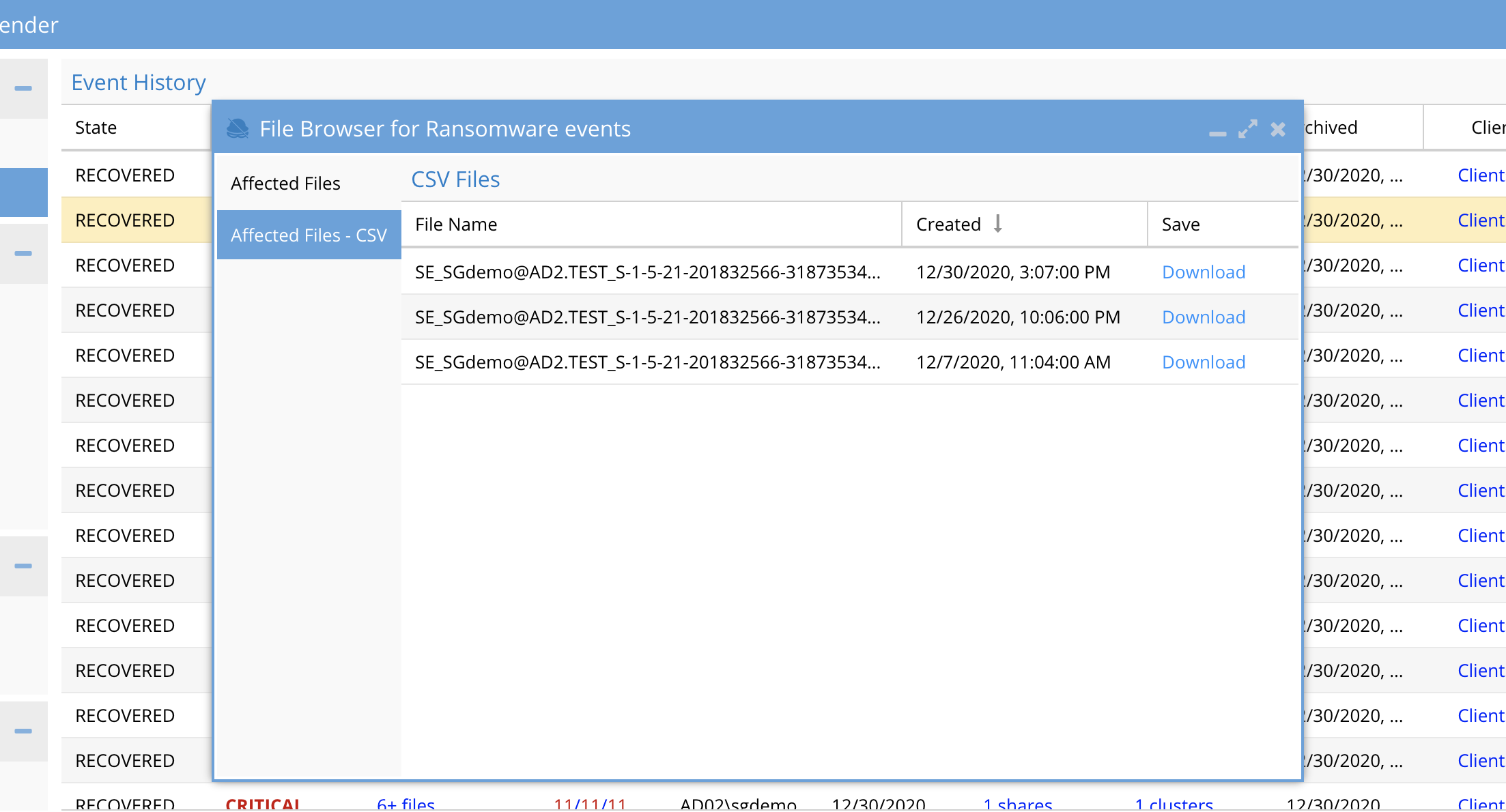
Files and CSV Download Column Ransomware Active Events
- The files section allows browsing of files that triggered the detection. A CSV download option provides a historical file list that contains all files from all detections for the specific user. This provides a history for all files that triggered events for each user when they have had multiple detections. The files will rollover and maintain a current file and then historical files will be listed with a data and time stamp.
- NOTE: The CSV rows will list signals , not files in each row. The files column cell for each row in the csv will list all files related to the signal. If using Excel double click the cell to see the list of files for that signal. Remember a signal is a pattern of user behavior that affects multiple files.
- The CSV will store the first 1000 files associated with detection, and there can be more files related to a detection that will not be stored in the CSV. The CSV could get very large to store all files so only the first 1000 are stored.
- In most cases, the CSV will store all affected files; it is best to use Easy Auditor to run a user report to get a complete list of files touched by a user.
- Each CSV file from ransomware defender “Active events” and “Event history” can only be downloaded within 28 days (4 weeks) from the file creation.
Threat Detection Signal Strengths in Ransomware Active Events
Threat detection Signal Strength is a measure of the severity of a user's File Event behavior. The higher the count the higher the severity of the detection.
The Signal Strength is displayed in the Eyeglass Ransomware Defender window Active Events or Event history tab.
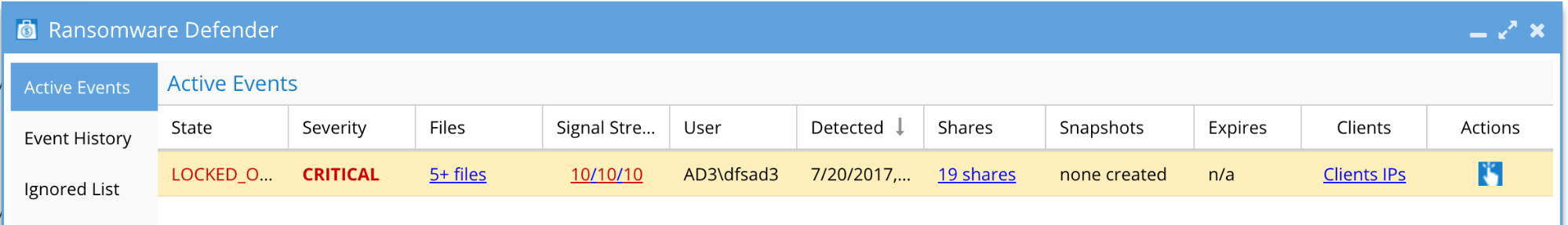
The numbers represent the peak of Warning, Major, and Critical signal strengths that were recorded in the entire lifetime of the Ransomware event. In addition, a list of shares by cluster and access zone is listed that have lockouts applied.
Signal Strength Window In Ransomware Active Events
When clicking on the Signal Strength in Eyeglass, you can see the threat detectors that contributed to the event. Note that this is not broken down by severity, and represents the total of the Threat Detector types that were tripped throughout the lifetime of the event for this user security event. These are not documented and are for support only.
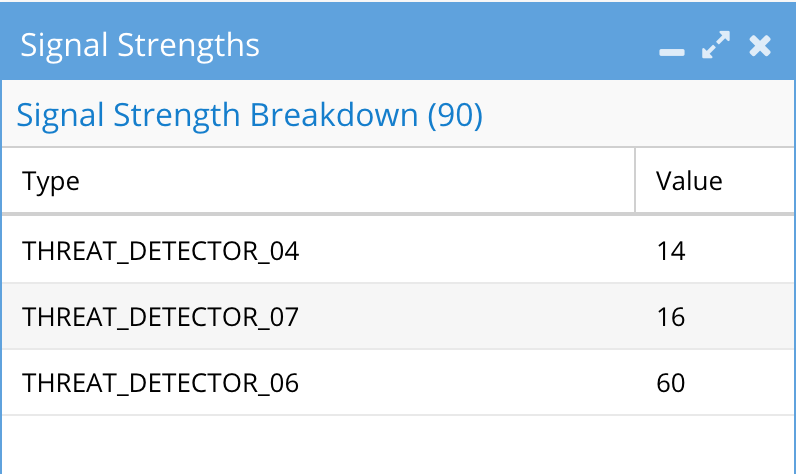
Note that the sum of these values can be greater than the peak signal strengths described above since it’s possible that the lifetime of the Ransomware event is greater than the interval for the thresholds.
© Superna Inc